71 min
Presentation of MOC/NOC/VOC/SOC/*OC
58 min
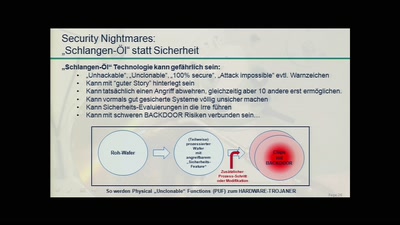
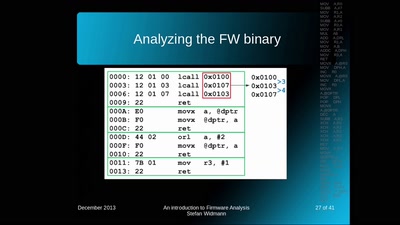
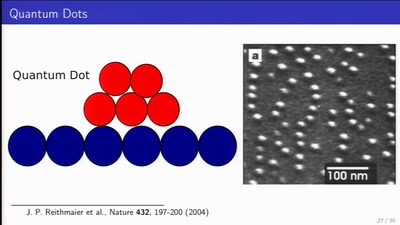
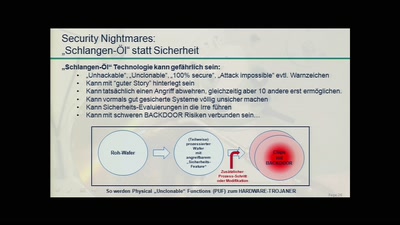
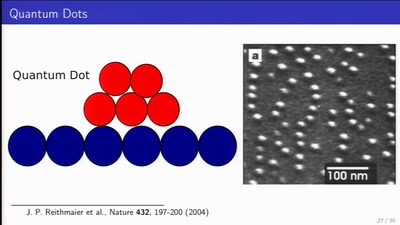
Physically Unclonable Functions for Hardware Tamper…
90 min
Damit Sie auch morgen schlecht von Ihrem Computer träumen.…

62 min
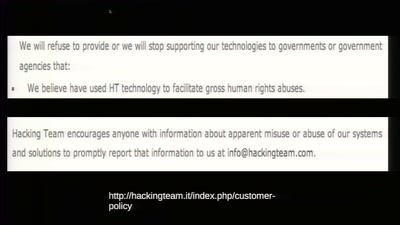
The militarization of the Internet
63 min
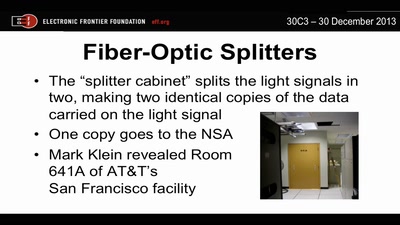
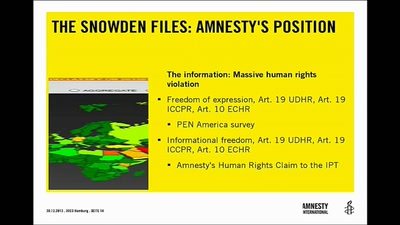
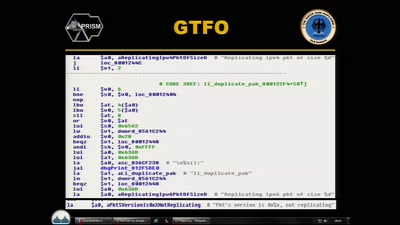
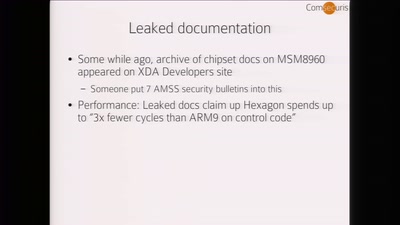
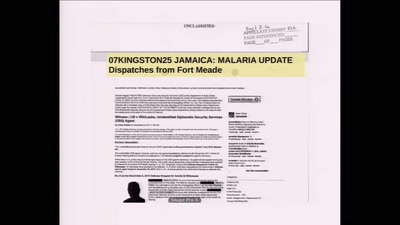
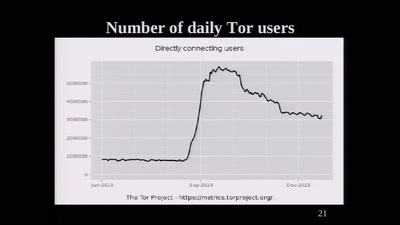
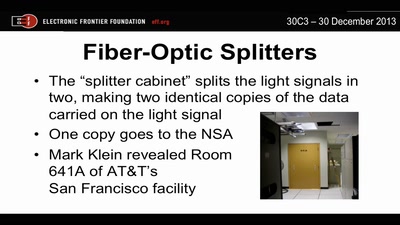
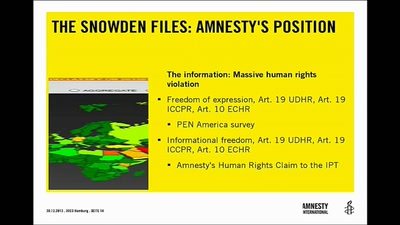
Everything we know about NSA spying
32 min
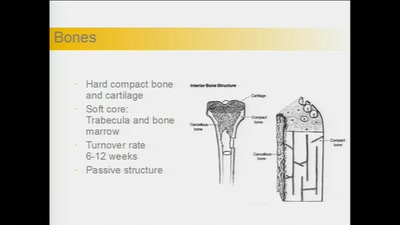
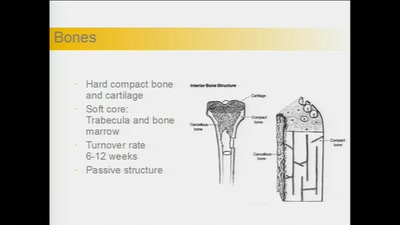
How to decipher the messages of your body

39 min
A parliamentary drama of 223 actors
32 min
"A New Hope" or "The Empire Strikes Back"?
60 min
getting out of surveillance state mode

61 min
Auf dem Weg zu fairer Elektronik am Beispiel der Elkos …
30 min
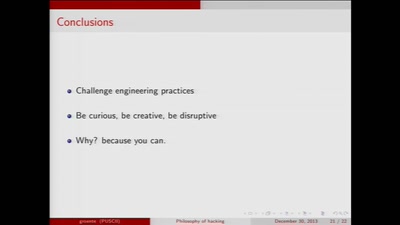
Contemplations on the essence of hacking and its…
45 min
The militarization of the Internet

117 min
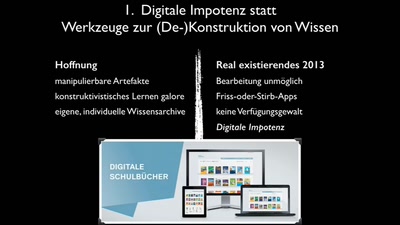
Der schonungslose Realitätsabgleich mit…

24 min
Terror, whistleblowers, drugs, internet
26 min
Using random sampling, entity resolution, communications…
66 min
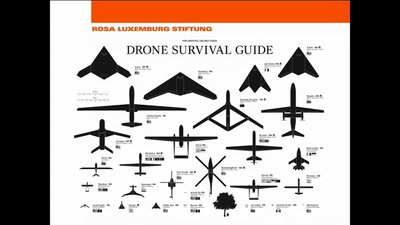
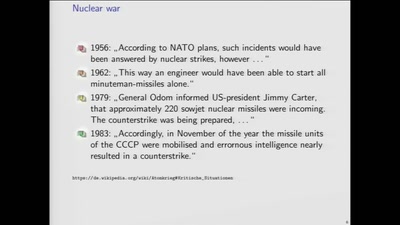
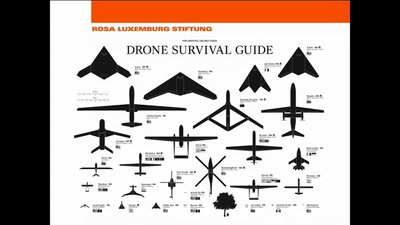
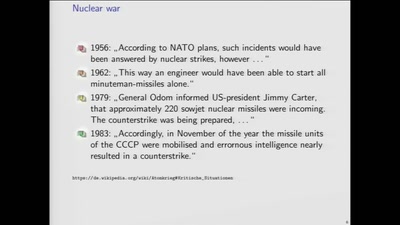
Kriegsführung der Zukunft?
62 min
Creating Internet Privacy and Security Resources That Don't…
42 min
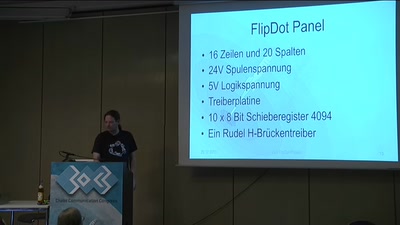
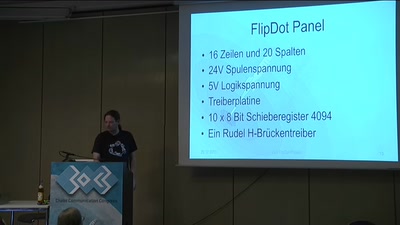
Spaß mit mechanischer Anzeige
29 min
30C3S SCE mbH: GEMA-Konkurrenz für Fortgeschrittene
56 min
what is the winning move?
31 min
Spending a year coding in a newsroom
46 min
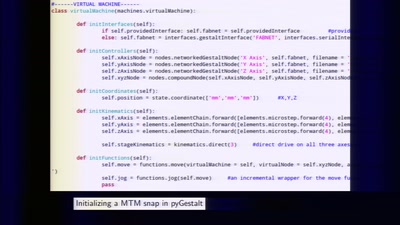
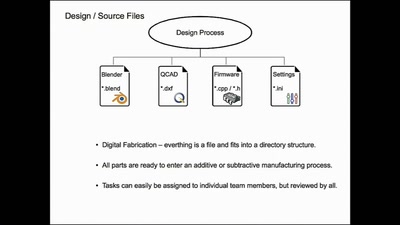
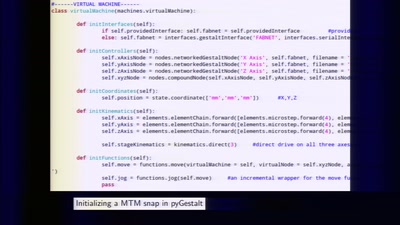
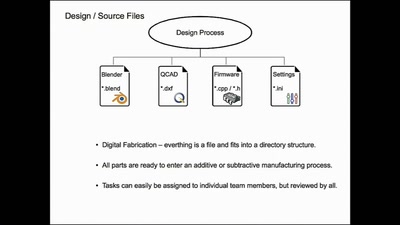
rapid prototyping of digital fabrication and…
60 min
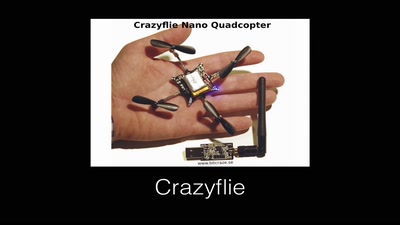
Autonomous flying vehicles, where are we and where are we…
62 min
Building a space for grassroots sustainable technology…
30 min
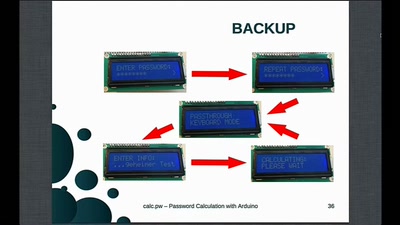
Passwortgenerierung mit Arduino [Generating passwords with…
33 min
experiences from the “i3 Berlin” 3D printer project with…
39 min
In China Your ID Card Knows Everything
55 min
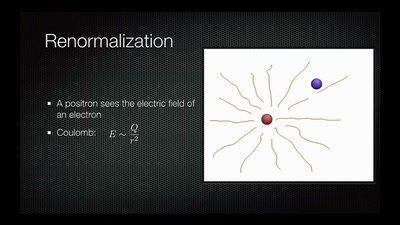
Artificial Intelligence Reloaded
59 min
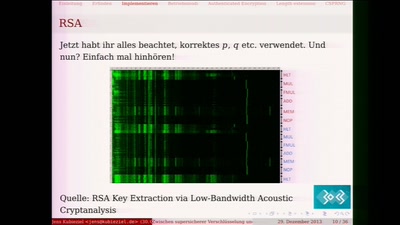
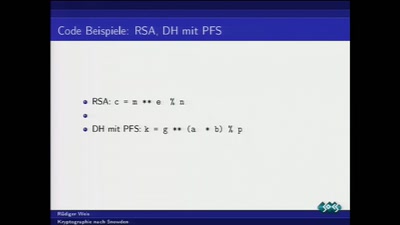
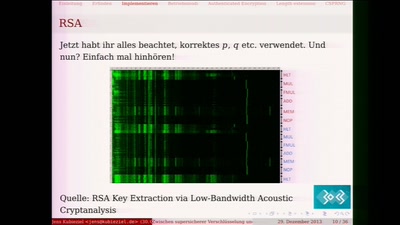
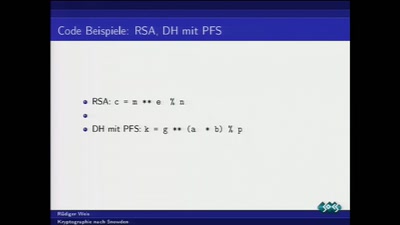
Ein Streifzug durch die Fehler in der Kryptografie

65 min
Eine Einführung in die Wirkungsweise psychedelischer…
47 min
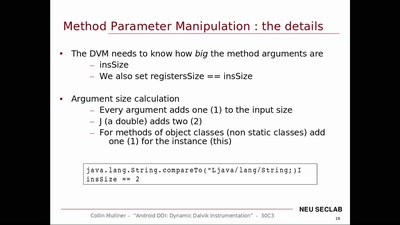
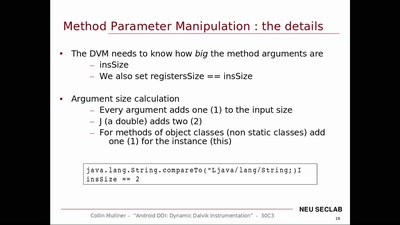
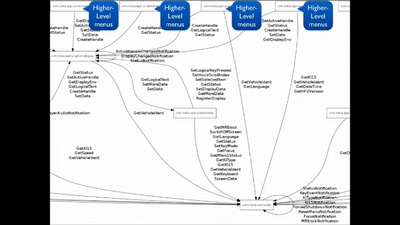
Dynamic Dalvik Instrumentation of Android Applications and…
58 min
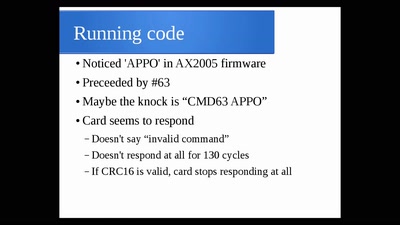
Hacking City-Wide Access Control Systems
30 min
An Arduino Powered Electric Guitar
33 min
!Mediengruppe Bitnik about their recent works
61 min
Von der Historie zur Zukunft
60 min
Fun and frightening uses of always-on camera enabled…

59 min
The future of IC analysis

41 min
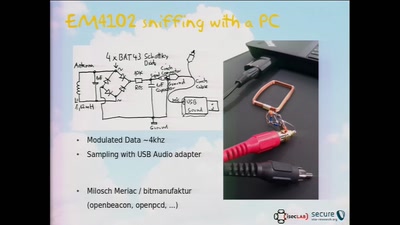
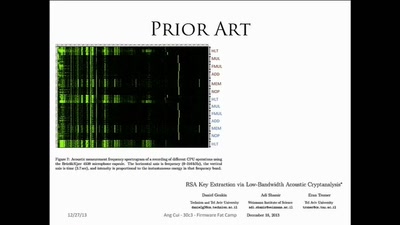
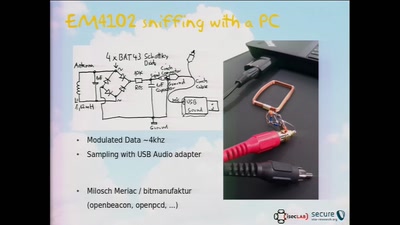
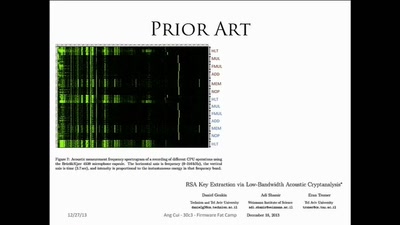
Side-Channel (and other) Attacks in Practice
49 min
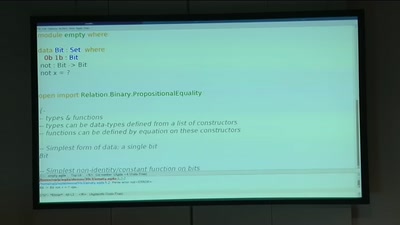
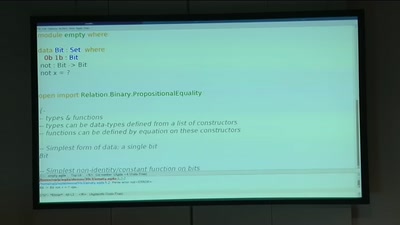
Security notions, proofs and attacks using dependently…

55 min
Attribute Based Credentials in Practice
29 min
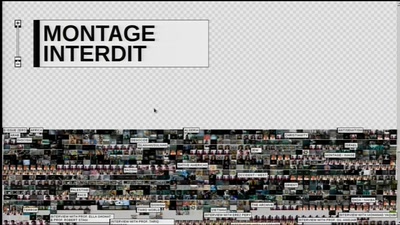
Creating mash-up movies by hidden activity and geography of…
26 min
Twisting time and space to explore the unknown
26 min
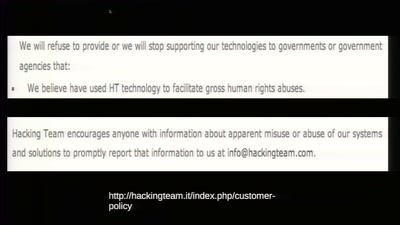
How technology is used to subvert and circumvent…
44 min
Pragmatic Advice for Security Researchers
60 min
A farewell to a bold proposal?
60 min
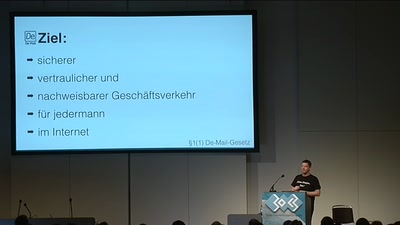
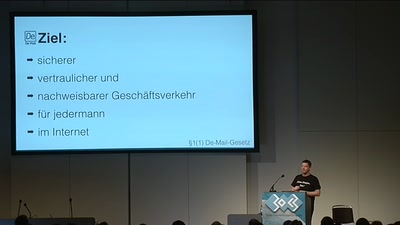
So hosten Sie Ihre De-Mail, E-Mail und Cloud direkt beim…
54 min
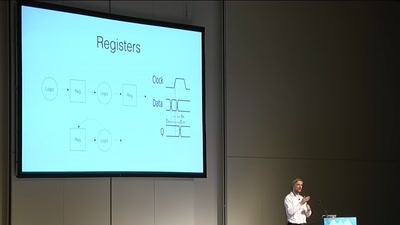
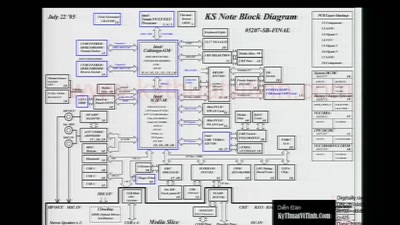
Making awesome stuff with FPGAs
57 min
How to make art after Snowden?
64 min
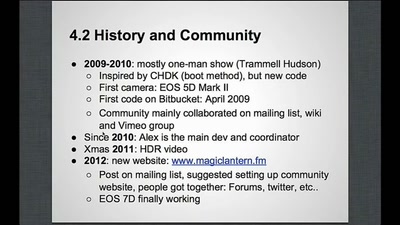
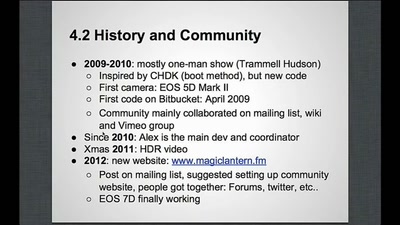
Free Software on Your Camera
61 min
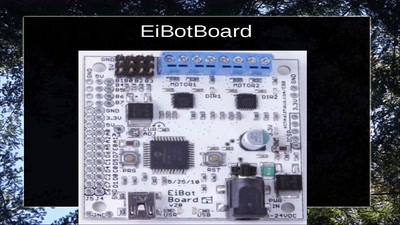
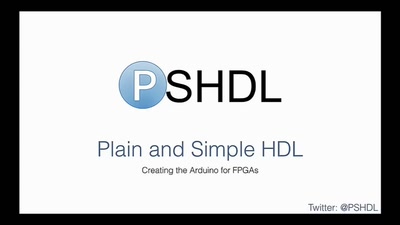
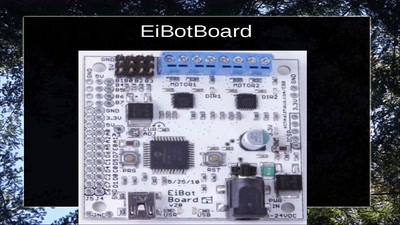
Let's create the Arduino for FPGAs

33 min
call for participation in project and product development
26 min
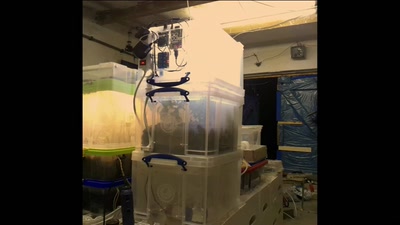
Food replicating Robots from Open Source Technologies
58 min
Using existing hardware platforms to integrate python into…
33 min
What can be done to protect the term, the notion and the…
64 min
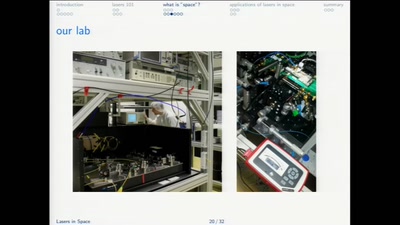
A case for expansionistic space policy
47 min
Repurposing an Inmarsat Dish
54 min
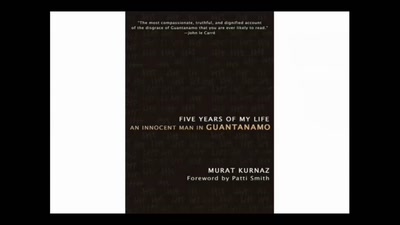
Art Practice under the Regime of Anti-Terror Legislation
147 min
Zahlenraten für Geeks [Number guessing for geeks]
58 min
Reporting on the secret trial of Chelsea Manning

66 min
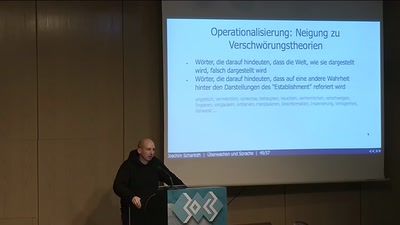
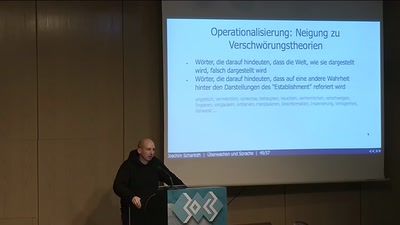
Die Diskussion um NSA, PRISM, Tempora sprachlich und…
54 min
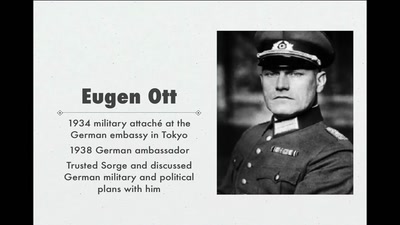
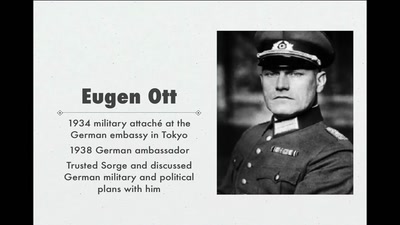
Stalin's best men, armed with paper and pen
62 min
We're living in interesting times

60 min
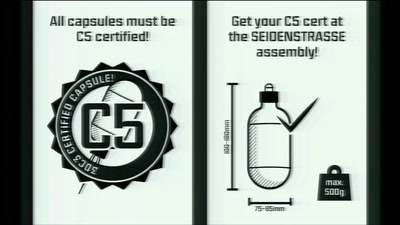
Welcome to the 30th Chaos Communication Congress

29 min
On Freedom of Facial Expression
57 min
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
47 min
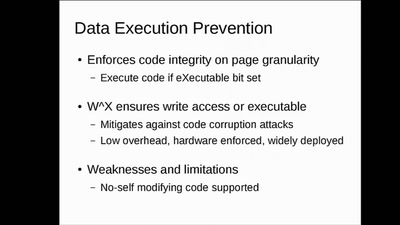
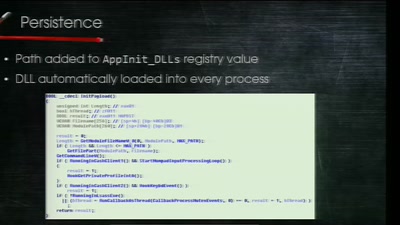
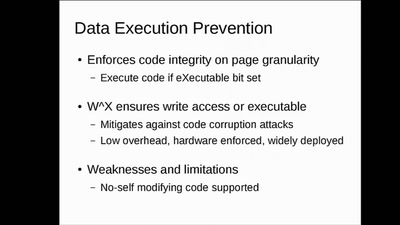
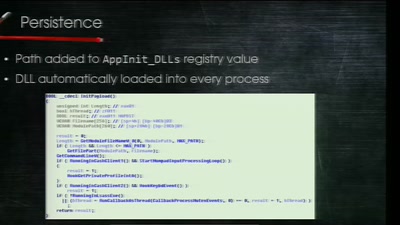
Clean boot every boot - rejecting persistence of malicious…
42 min
Embedded Security Using Binary Autotomy
38 min
Velocipedes and Face Recognition

36 min
A singing and dancing robot build to take part in casting…
46 min
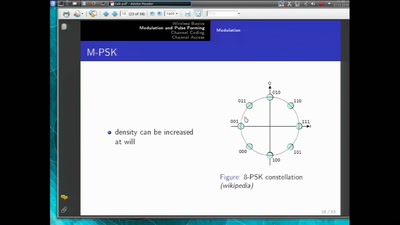
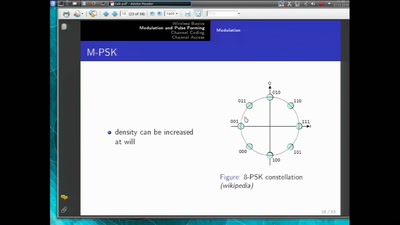
introduction to software radio principles
40 min
Techniques - Tools - Tricks

45 min
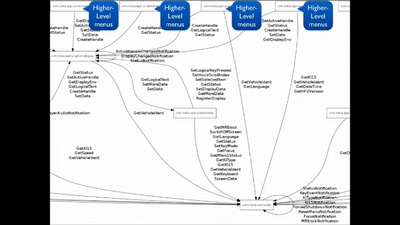
Deep program analysis without the headache
60 min
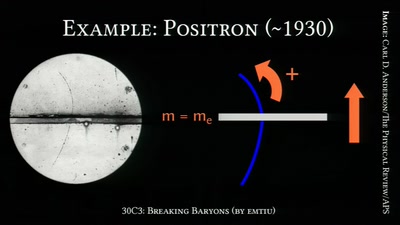
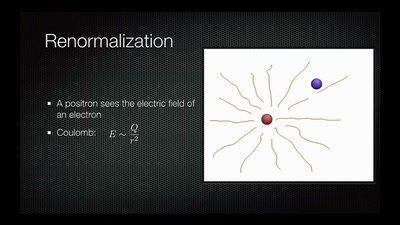
On the Awesomeness of Particle Accelerators and Colliders
58 min
How to do things with words
47 min
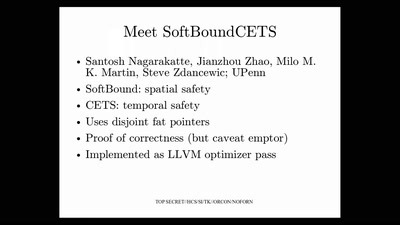
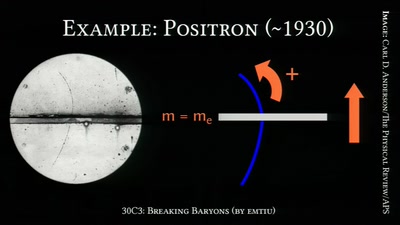
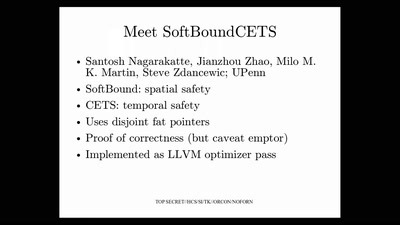
Applying science to eliminate 100% of buffer overflows

54 min
Wer kontrolliert das Netz?
56 min
Introduction to Heterogeneous Parallel Programming
28 min
Erkenntnisse aus Informationsfreiheitsanfragen - Hacks,…
36 min
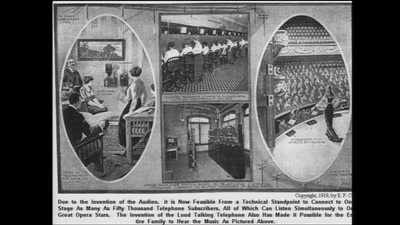
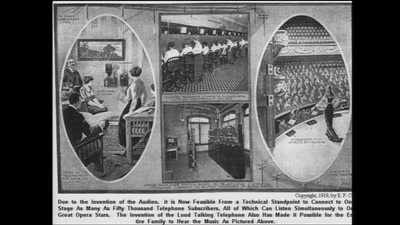
Concepts and components for intercontinal communication…

45 min
OMG - my Smart TV got pr0wn3d
56 min
Stealing Money from ATMs with Malware
51 min
A Decentralized PKI For Social Movements
48 min
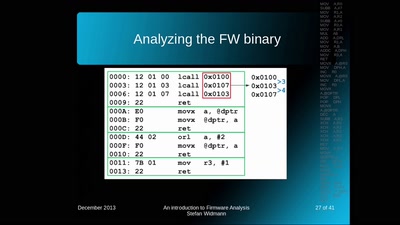
How OpenWrt evolved from a WRT54G firmware to an universal…
49 min
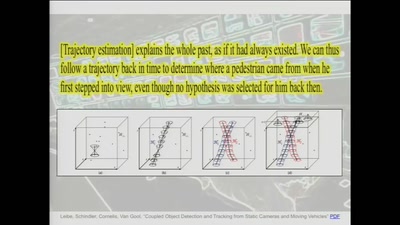
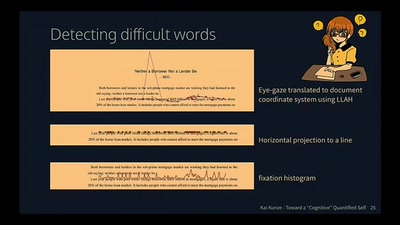
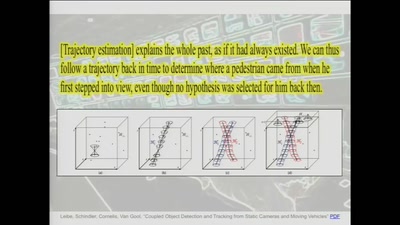
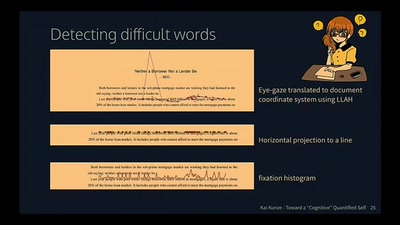
Activity Recognition for the Mind