Search for "Jan Ole"
prev
next
21 min
Are you sick of editing 8 files, and loading 5 daemons, for…
58 min
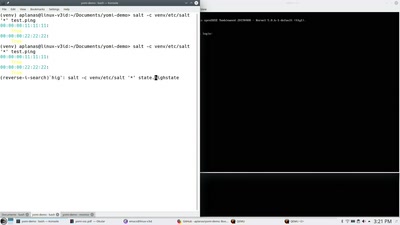
Using Salt as an alternative to AutoYaST

50 min
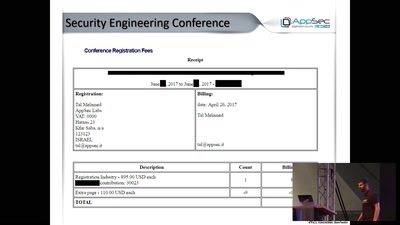
Not only hackers do Security, Privacy and Hacking. Want to…

47 min
Learn about the building blocks of a network application
61 min
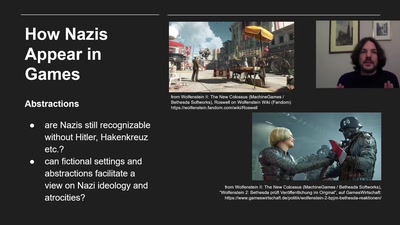
Depiction, Normalization, Consequences
56 min
Hacking BLE Smart Devices

50 min
or Any Other Catastrophe-Movie
51 min
Elevated to the Next Level
9 min
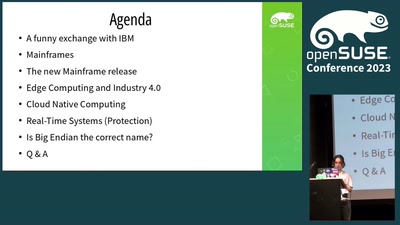
Is Big Endian continously the right name?
41 min
Security Of Railway Communication Protocols
prev
next