70 min
Was Sie schon immer nicht über darüber wissen wollten wer…
41 min
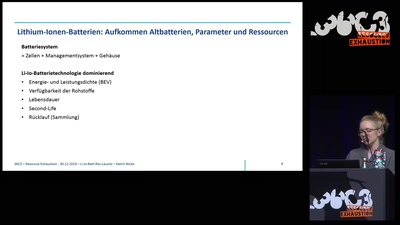
Eine industrielle Perspektive für die Lausitz?

40 min
Best of Informationsfreiheit

61 min
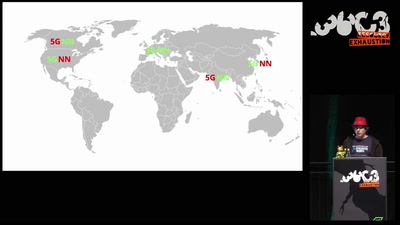
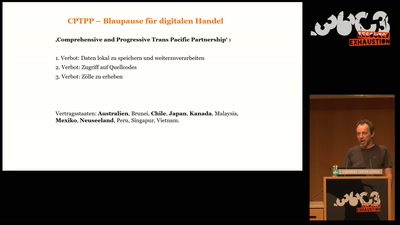
In welcher digitalen Welt werden wir leben?
38 min
Governments around the world are implementing digital…
40 min
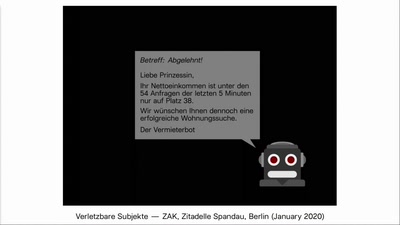
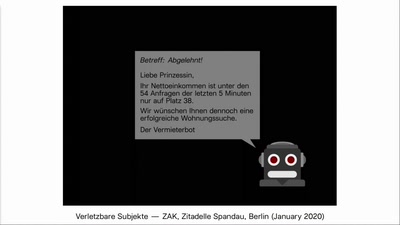
A media-art project which automates the search for flats in…
35 min
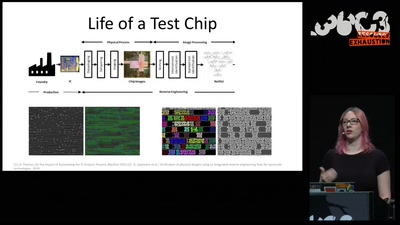
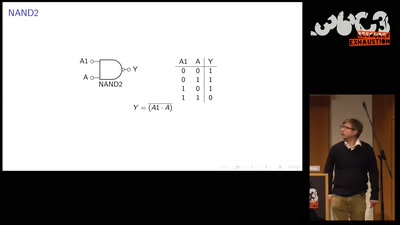
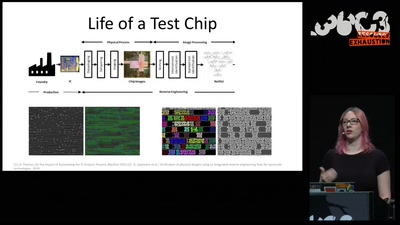
Introduction to IC reverse engineering for…
64 min
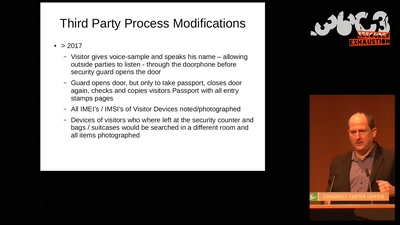
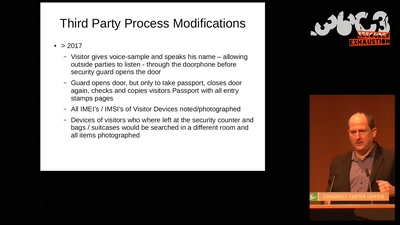
Details about the man hunt for Julian Assange and Wikileaks
41 min
Resilient. Trustworthy. Sustainably Open.
43 min
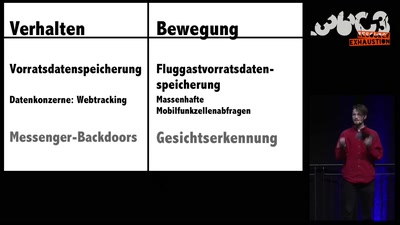
How to Stop the Dubious Use of Passenger Name Records by…
38 min
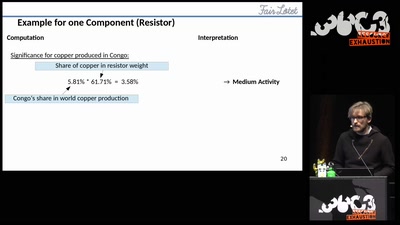
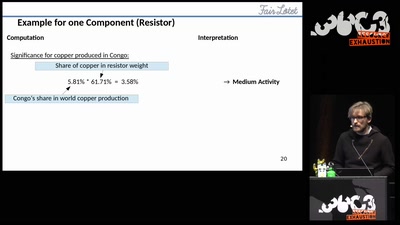
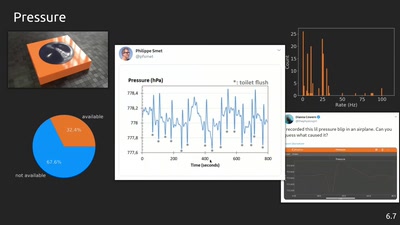
A Tool for Analyzing the Fairness of Electronic Devices
38 min
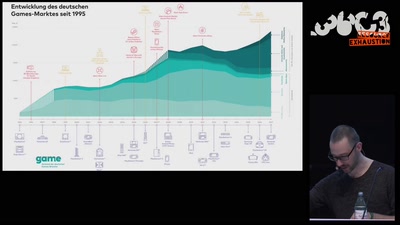
Makroökonomische Auswirkungen der Digitalisierung auf den…

60 min
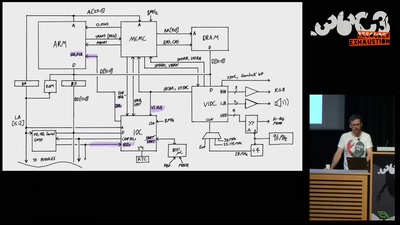
A dive into the foundations of hardware reverse engineering…

50 min
The sumo robot fight for the technically ungifted
42 min
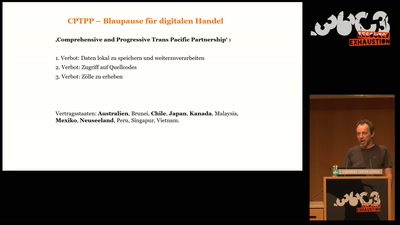
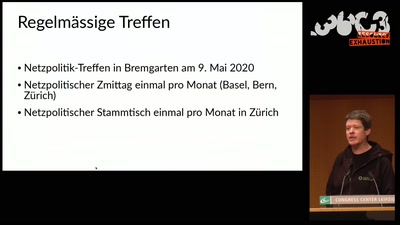
Status of the Net Neutrality Reform in Europe

38 min
EU plans to swipe our freedom of expression under the carpet
113 min
8 Mikrokosmen, 8 Expert*innen, je 8 Minuten zu…
41 min
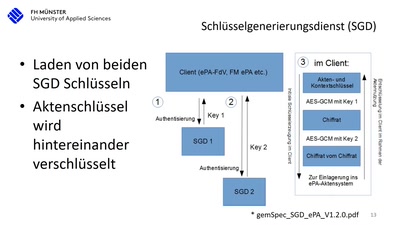
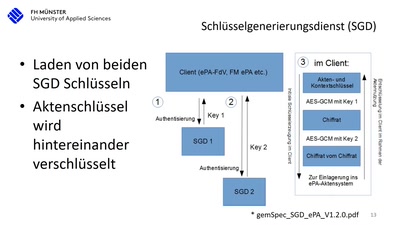
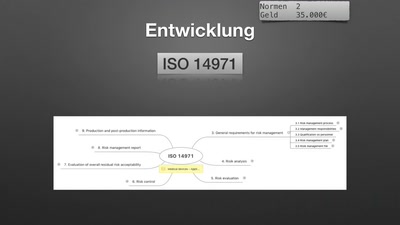
Die Realität beim Arztbesuch nach 15 Jahren Entwicklung…

43 min
Strategies and tactics to ‘hack’ public spaces and social…

37 min
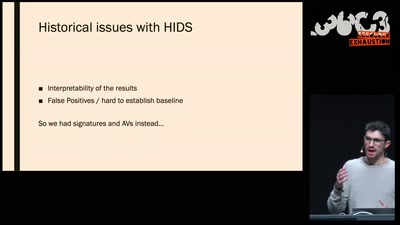
Don't ask what you can do for TPMs, Ask what TPMs can do…
40 min
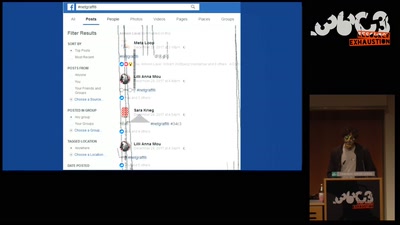
Graffiti in the ruins of the feed and the…
43 min
Menschliche Faktoren der IT-Sicherheit

39 min
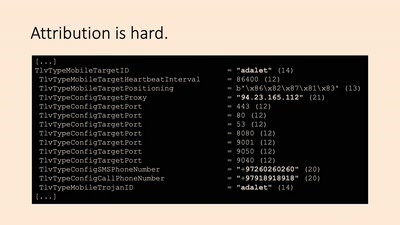
Egypt's Civil Society Under Attack
40 min
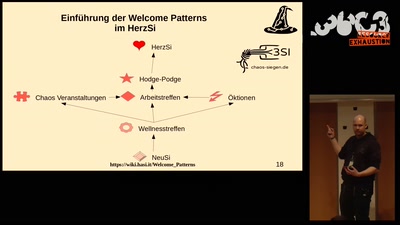
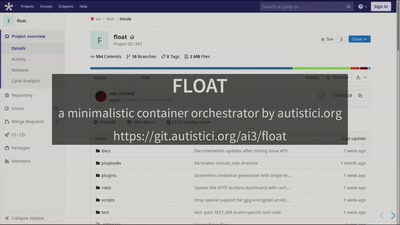
Human agreements, comunication infrastructures, services in…
38 min
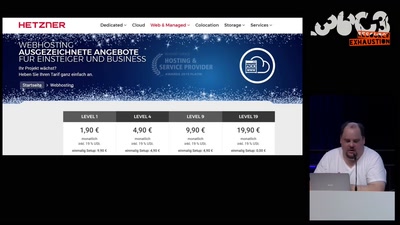
Warum unser Web nachhaltiger werden muss und wie wir das…
40 min
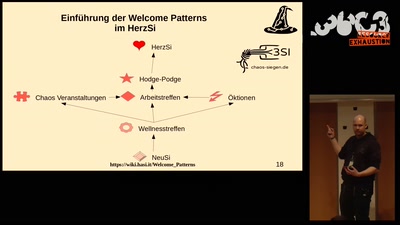
(Eine Gemeinschaftsproduktion der Haecksen, der…

40 min
War alles schon mal besser
60 min
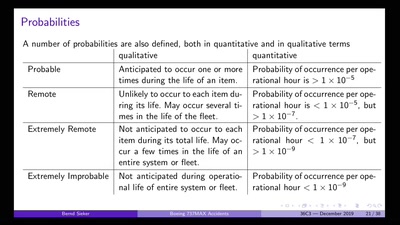
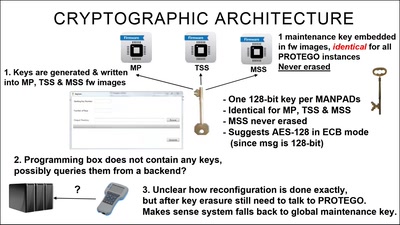
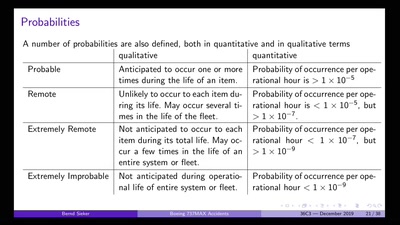
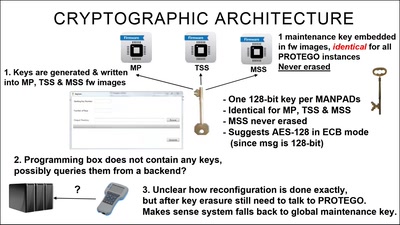
Underestimating the dangers of designing a protection system
62 min
Social, artistic & theoretical experiments with…
62 min
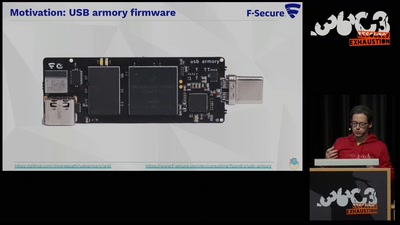
Auditing Boot Loaders by Example
61 min
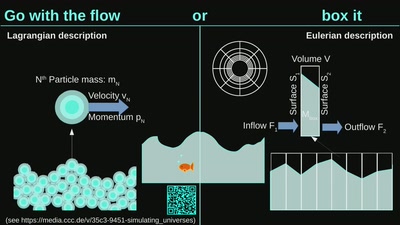
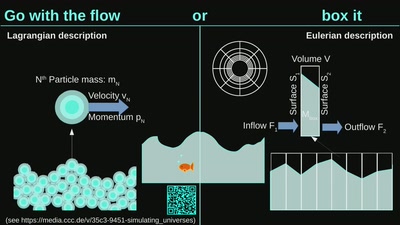
How simulations help us understand the Universe
52 min
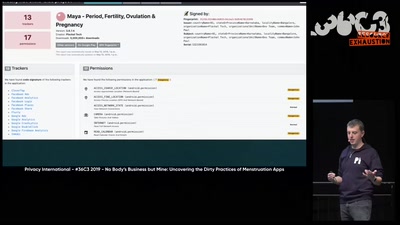
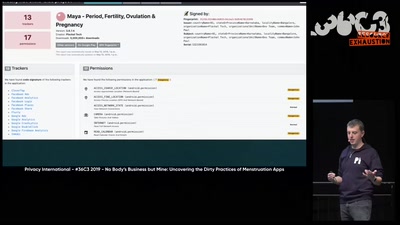
The Not-So Secret Data Sharing Practices Of Menstruation…
63 min
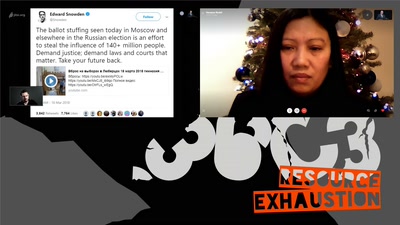
Whistleblowers and the Cases of The Snowden Refugees and…
61 min
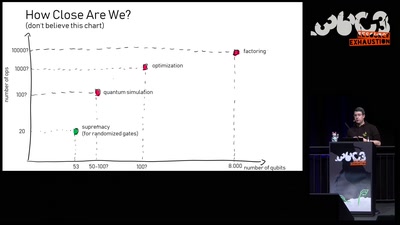
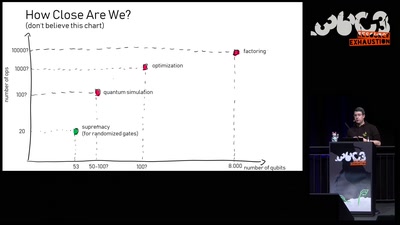
An introduction to quantum computing and a review of the…
59 min
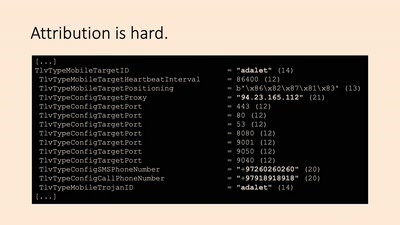
Rechtsbrüche beim Export von Überwachungssoftware
62 min
Mit künstlicher Intelligenz zu neuer Kunst zum…
42 min
How to convert standard wifi dongles into digital broadcast…
53 min
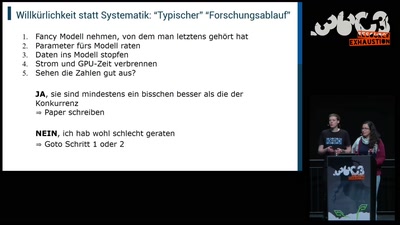
An introduction without maths
64 min
Warum wir zivilen Ungehorsam und Subversion mehr brauchen…
62 min
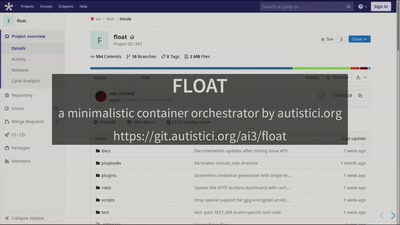
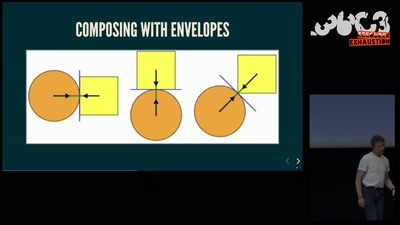
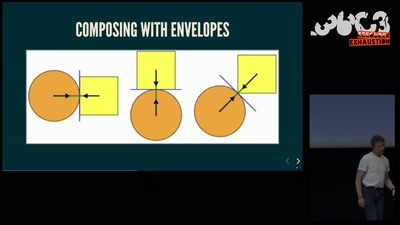
Evolve your hack into robust software!
50 min
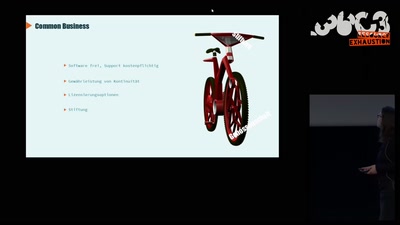
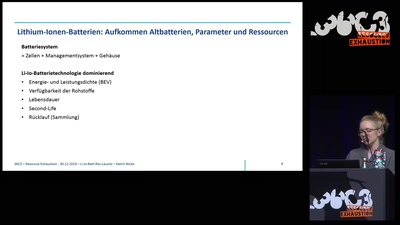
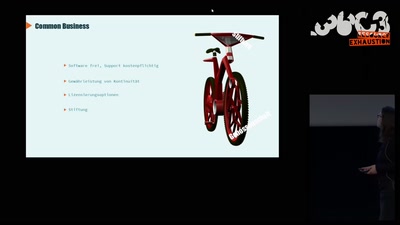
Von E-Bikes in der Connected Mobility zur Entstehung eines…
57 min
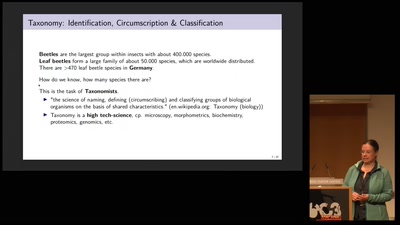
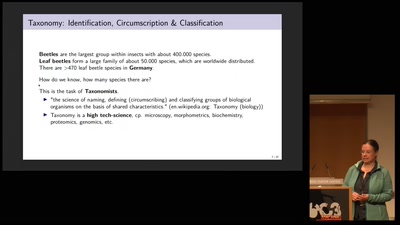
Conservation Genomics between Taxonomy, Big Data,…
44 min
Lesung des öffentlichen Sourcecodes
48 min
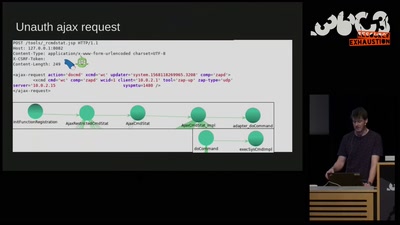
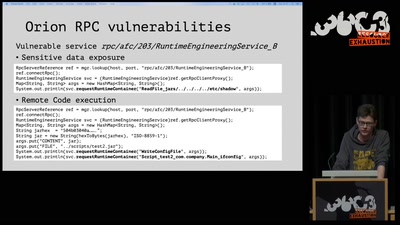
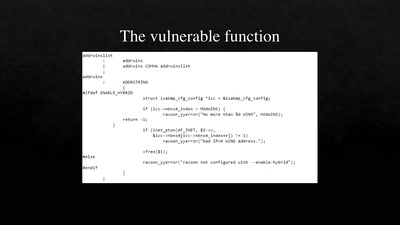
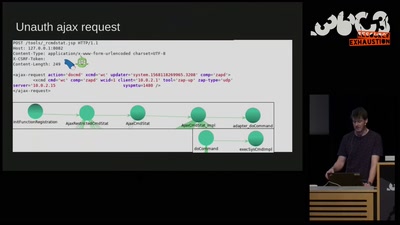
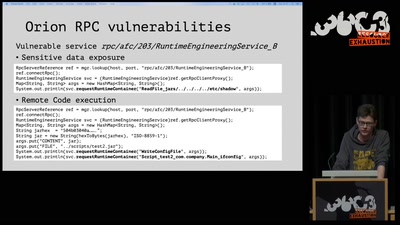
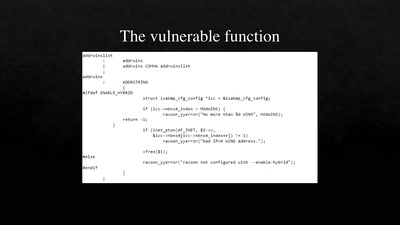
3 different RCE vulnerabilities on Ruckus Wireless access…
55 min
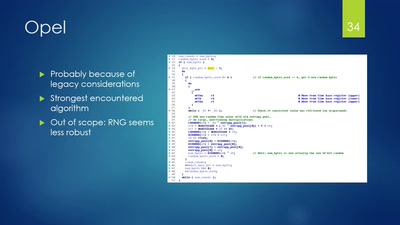
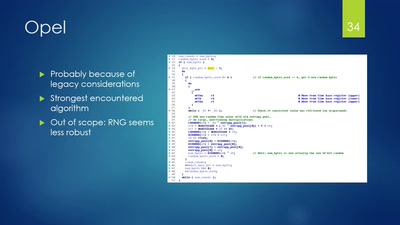
Uncovering and assessing a second authentication mechanism…
55 min
Leaking Your Recent Memory Operations on Intel CPUs
49 min
Be prepared for the coming Digital Winter. And play…
58 min
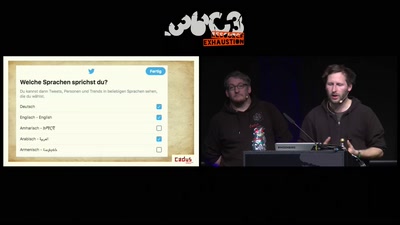
A rough guide to over-regulating free speech with…
59 min
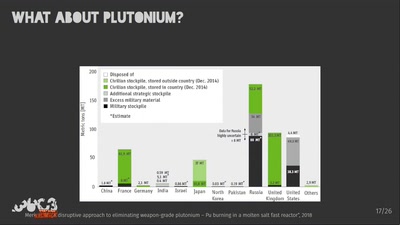
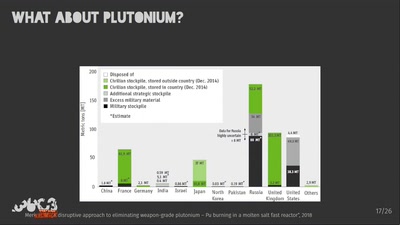
Military warheads as a source of nuclear fuel

63 min
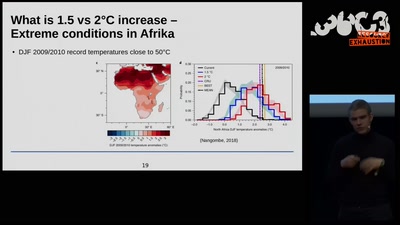
How to understand this historic challenge and what we can…
37 min
The Sound of Surveillance
40 min
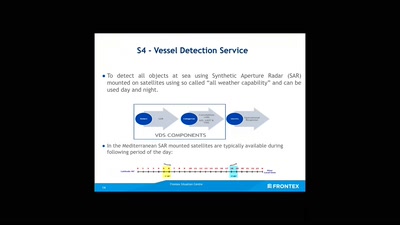
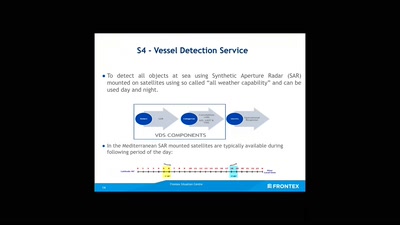
How an agency implements Fortress Europe by degrading…

41 min
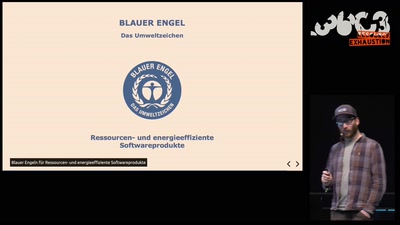
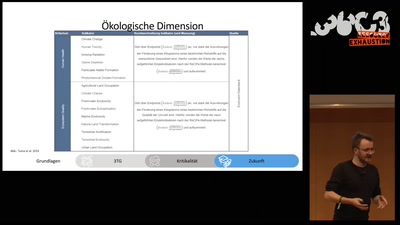
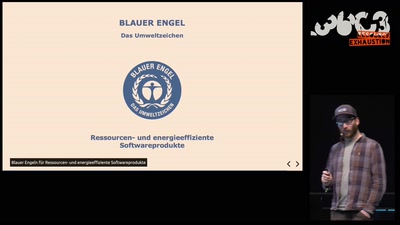
The environmental costs of digital industry and pathways to…
35 min
Taking a look at a covert CIA virtual fencing solution
42 min
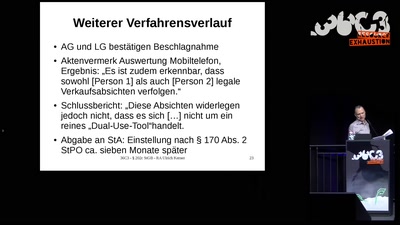
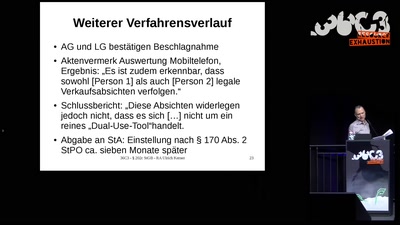
Cybercrime-Ermittlungen: Vorsicht vor der Polizei! Oder:…

43 min
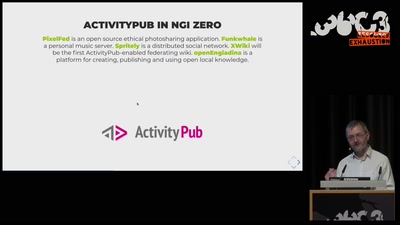
Challenges for distributed and decentralized technology…
41 min
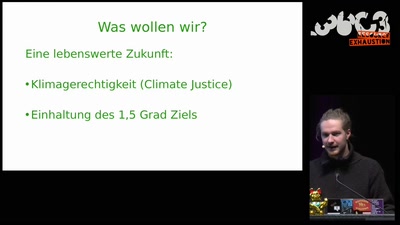
Schule schwänzen für das Klima
40 min
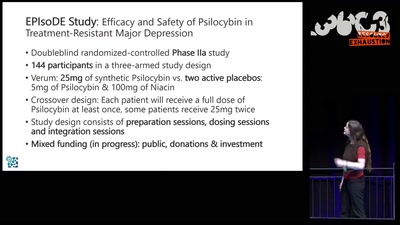
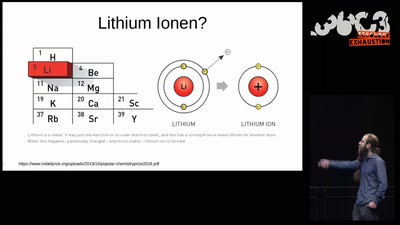
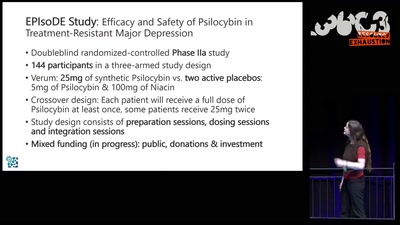
Psychedelic Therapy as a fundamentally new approach to…
58 min
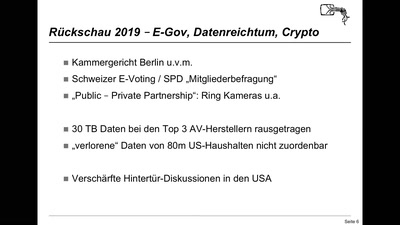
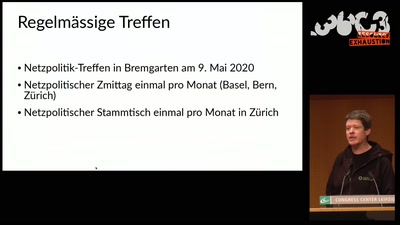
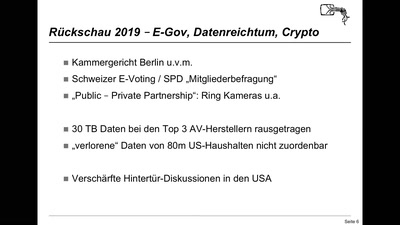
E-ID, E-Voting, Netzsperren und andere netzpolitische…
57 min
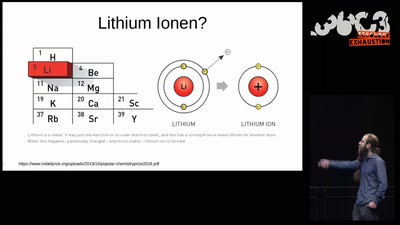
Hardware attacks on the latest generation of ARM Cortex-M…
64 min
Wie lange kann es so weitergehen?
63 min
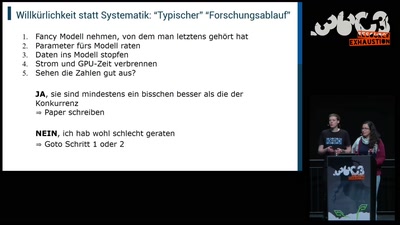
Können wir Software bauen, die nützlich /und/ unbedenklich…
61 min
How to understand the environmental impact of the digital…
59 min
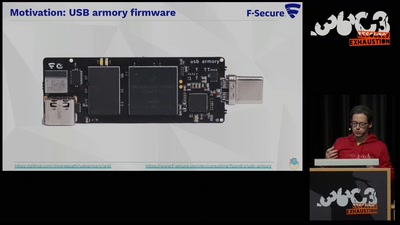
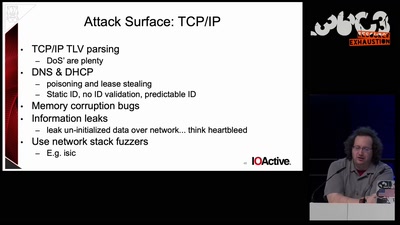
Reducing the attack surface with pure embedded Go.
55 min
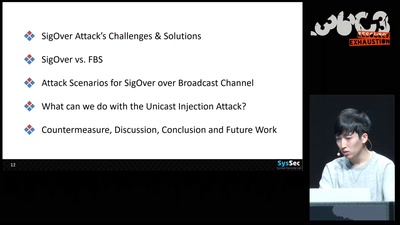
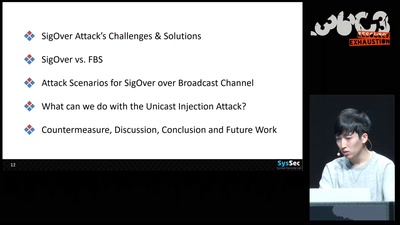
Signal overshadowing attack on LTE and its applications
60 min
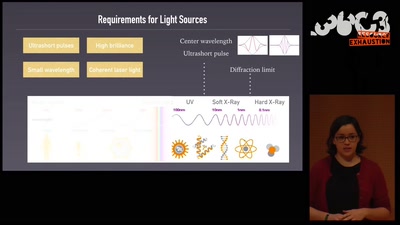
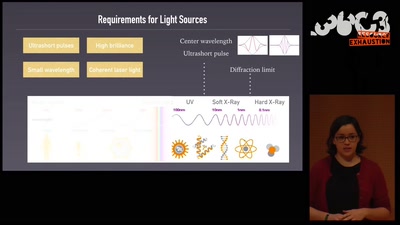
Featuring the shortest movies and the largest lasers
60 min
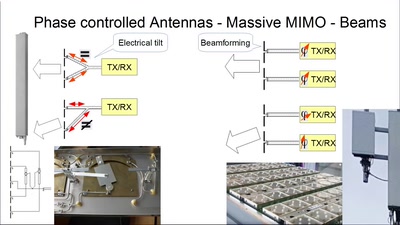
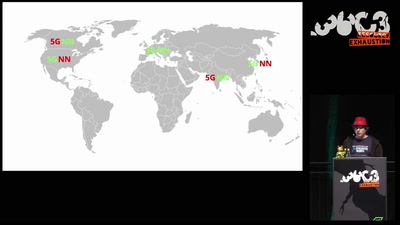
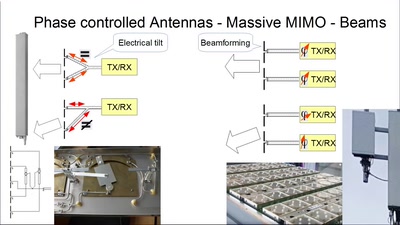
Die Luftschnittstelle und das Core im Wandel der Zahlen
63 min
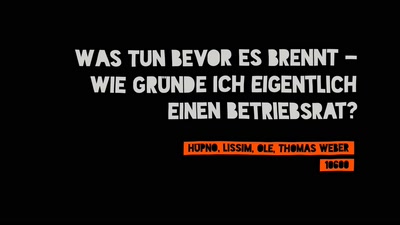
Wie gründe ich einen Betriebsrat, bevor die Kacke dampft?
60 min
A security study of turbine control systems in power…
46 min
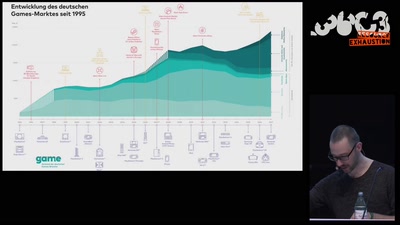
Wie die radikale Rechte (ihre) Politik gamifiziert
60 min
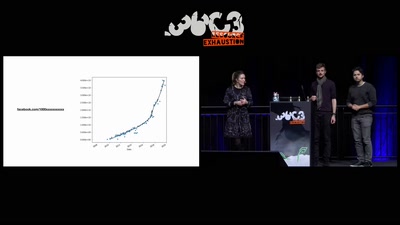
How thousands of Facebook, You Tube and Instagram pages…
58 min
Decoding The Cultures of Hacking One Video at a Time

46 min
--Gaining code execution using a malicious SQLite database
62 min
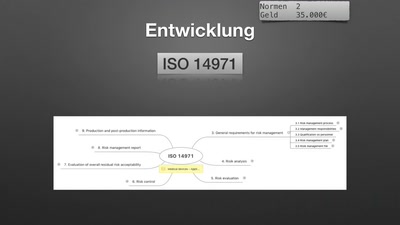
Was müssen Medizinproduktehersteller einhalten (und was…
63 min
Ein nicht nuklearer Blick auf das Ende der Welt
47 min
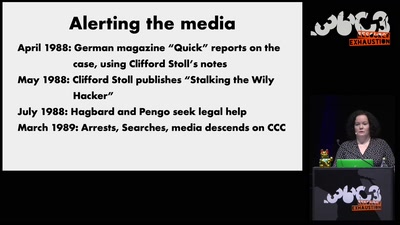
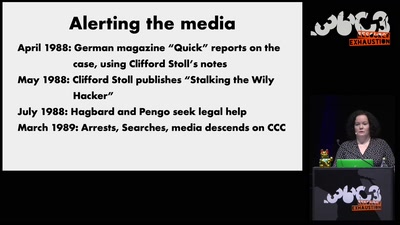
Looking back at the perhaps most dramatic instance of…
40 min
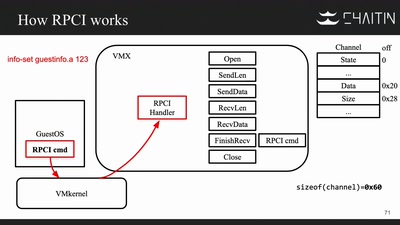
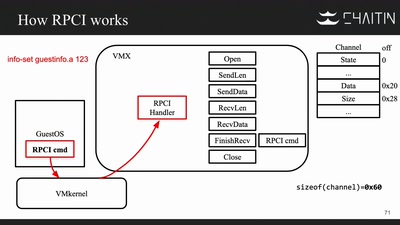
Breaking Out of a Sandboxed Virtual Machine
91 min
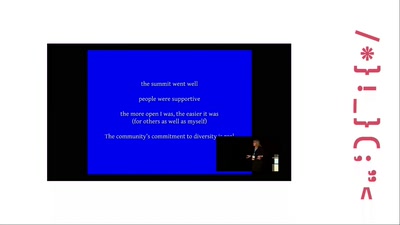
From Unanimity to Anonymity
63 min
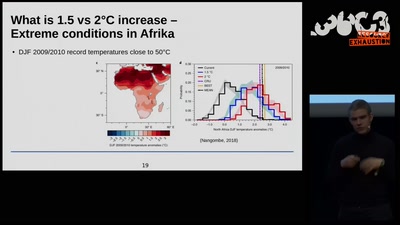
What we can and need to change to keep climate change low -…
55 min
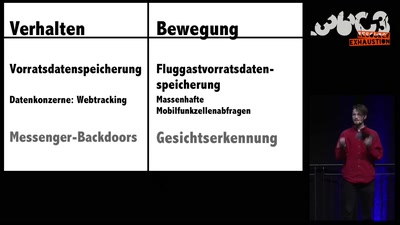
Von Handyauswertung, intelligenten Grenzen und Datentöpfen
60 min
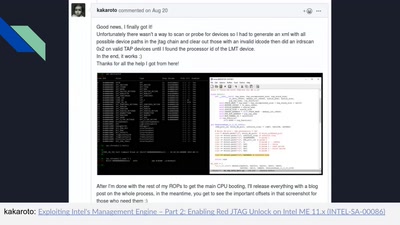
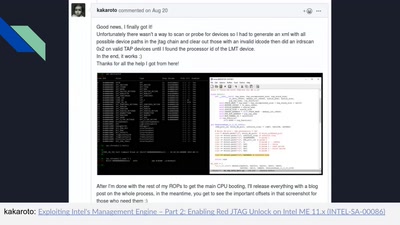
Understanding the ME at the OS and hardware level

52 min
A review of the best art & tech projects from 2019. With a…
46 min
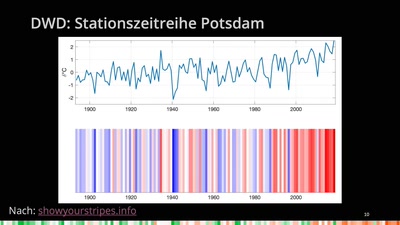
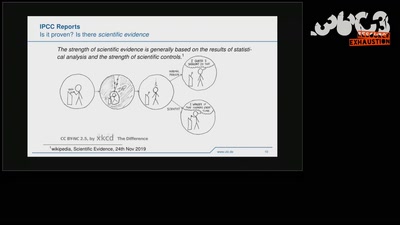
The Science Behind Climate Reports

54 min
Fables from building a startup in Silicon Valley
60 min
Pleiten, Pech und Pannen in der Zahlungsdiensteregulierung
58 min
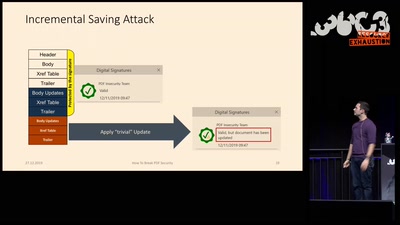
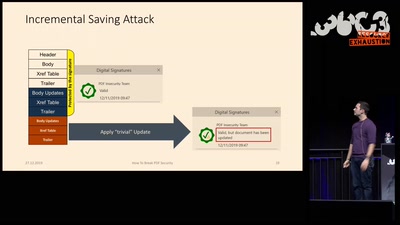
Breaking PDF Encryption and PDF Signatures
46 min
Exploring a new attack surface on the 3DS
58 min
Wohin eigentlich mit all der erneuerbaren Energie?
53 min
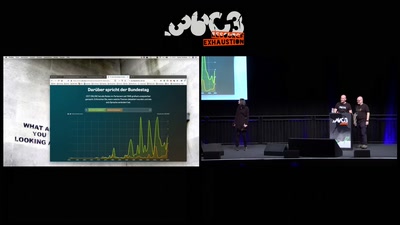
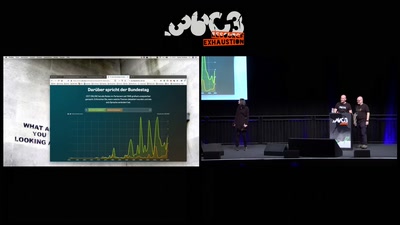
Gesellschaftlicher Wandel in den Reden im Bundestag
56 min
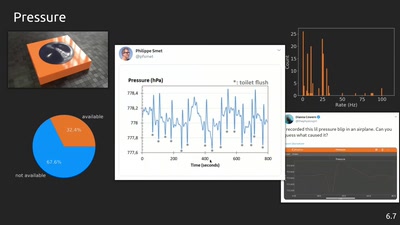
An open source project for education, research and tinkering
39 min
Spoiler: Apple is bad at patching
58 min
Einblicke in die Forschung und Ausblick in die…
60 min
Humanitäre Hilfe zwischen Propaganda, Information und…
58 min
Everything about the Archimedes computer (with zero…
52 min
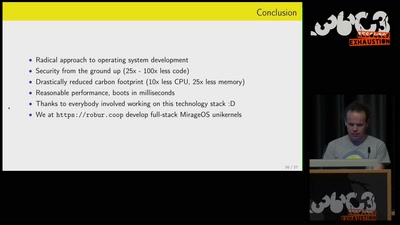
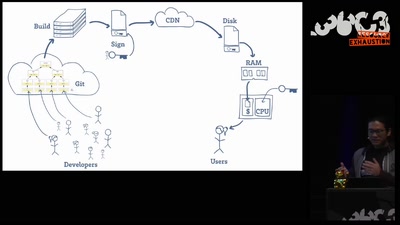
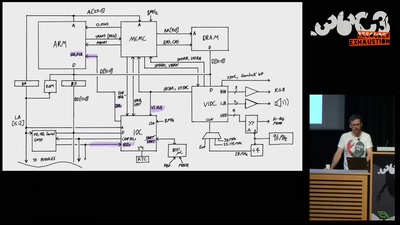
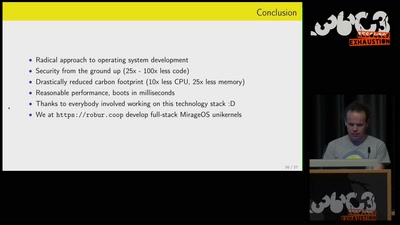
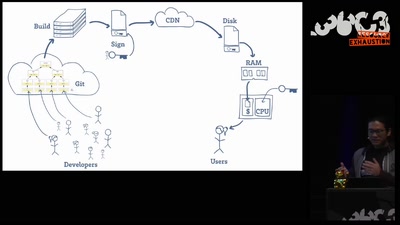
Reducing carbon footprint of network services with MirageOS…
60 min
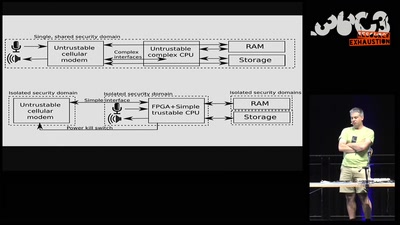
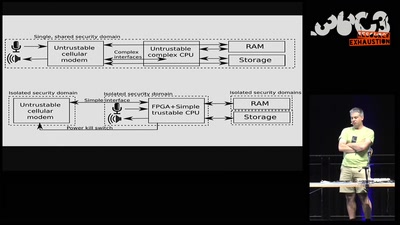
How Betrusted Aims to Close the Hardware TOCTOU Gap