34 min
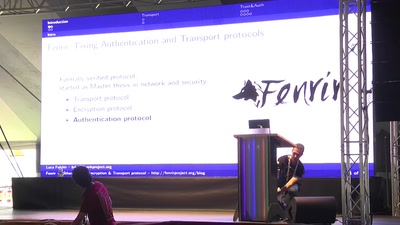
Fixing Authentication and Transport protocols
56 min
Hacking BLE Smart Devices
54 min
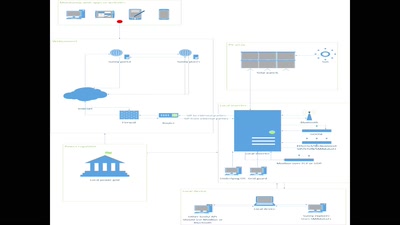
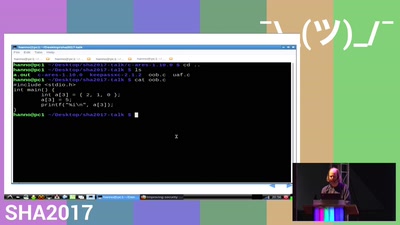
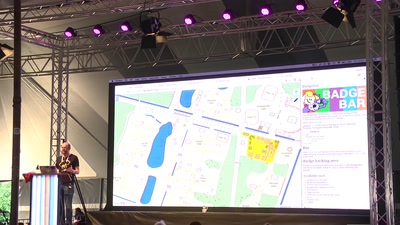
How all the infra teams made SHA2017 possible
61 min
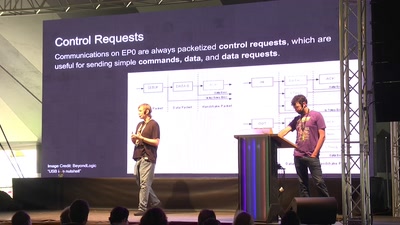
easy USB hacking, sniffing, and spoofing
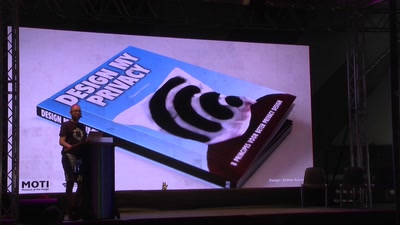
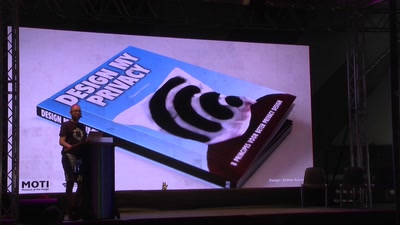
![NSFW: Di[CENSORED]s for privacy](https://static.media.ccc.de/media/events/SHA2017/49-hd.jpg)
28 min
Why not give hackers and agencies something to look at . .
29 min
Five days of hacking, this is what happened. You wouldn't…

25 min
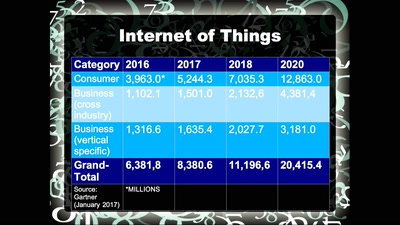
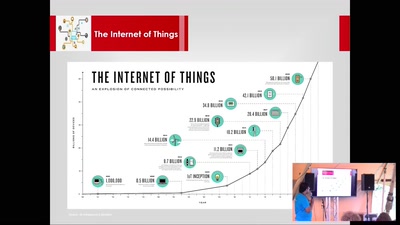
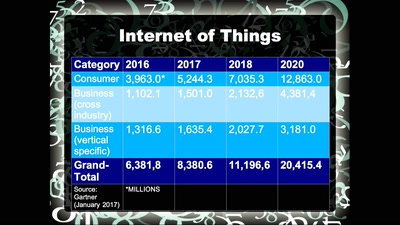
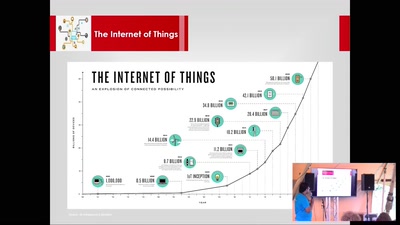
Everything is interconnected - but how?

57 min
Experiences with Aadhaar in India, or what possibly could…

36 min
How you can communicate, free running style, using nothing…
17 min
A documentary on privacy for the broad audience.
62 min
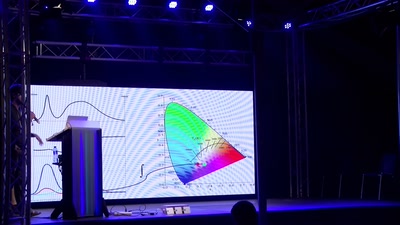
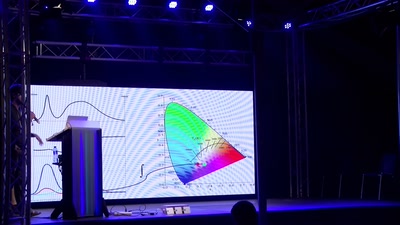
Adventures in LED Lighting
81 min
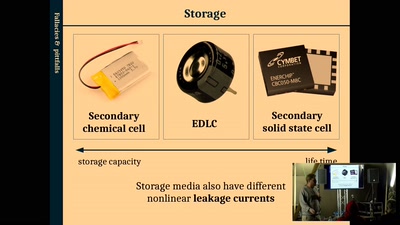
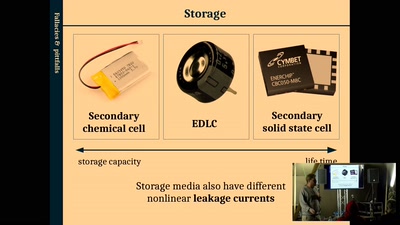
Towards a future of autonomous wireless electronics without…
58 min
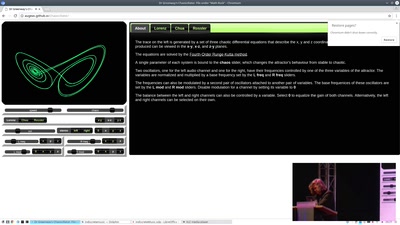
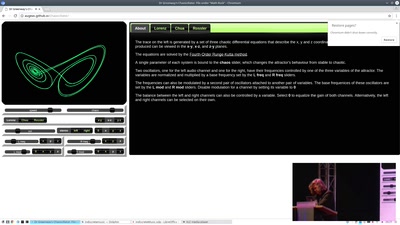
(mis)adventures in generative art
60 min
Internet Measurements' Ethical Dilemmas and RIPE Atlas
24 min
Story of a 15 year old hacker in collaboration with his…

44 min
Documenting digital culture through handwritten letters
51 min
What goes into playing defence and what can be holding you…
36 min
Bringing an electronic project to market in kit form
49 min
Implementing a Law to juridically, operationally and…

40 min
The ultimate Hackerspace; From Panopticon-prison to…
26 min
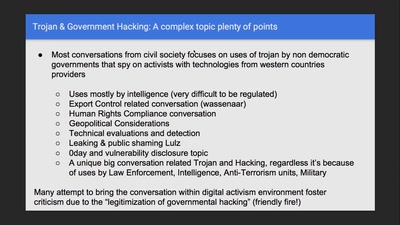
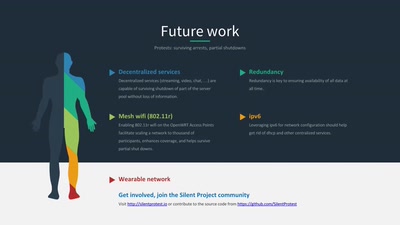
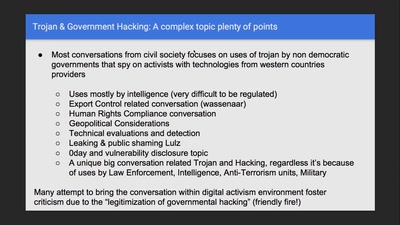
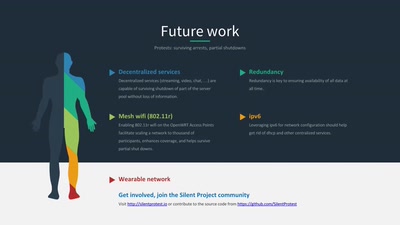
DIY wearable protest network
60 min
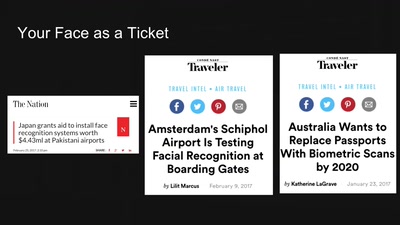
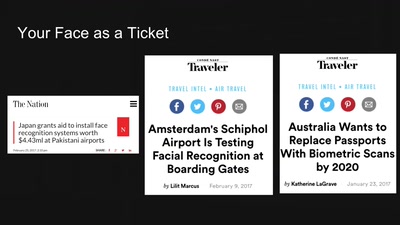
Identity and Agency In the Age of Algorithms
58 min
Theories of Governance for a Distributed Machine Vision…
35 min
Understanding and tools to mitigate network-scale violences
60 min
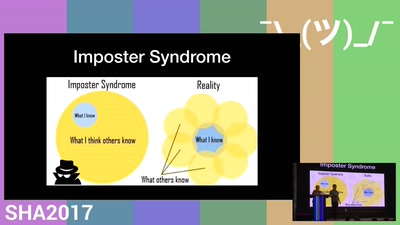
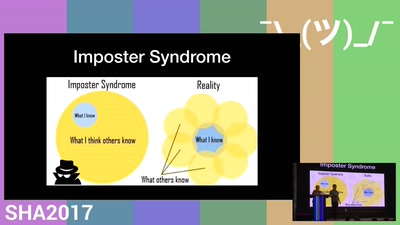
Managing Neurodiversity with Cognitive Empathy
30 min
Combining 3D printing and crystallisation techniques
56 min
From Napster to Bitcoin to Ethereum to Statebox: saving the…

21 min
Ethics, colonialism, technological optimism and the reality…
68 min
How to read brainwaves using cheap toys
49 min
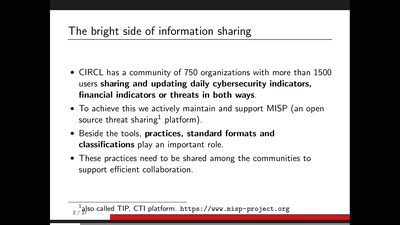
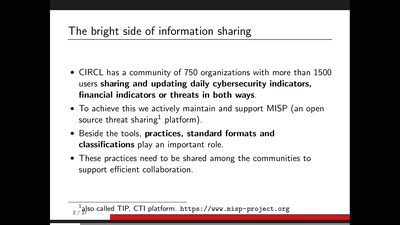
The MISP threat sharing platform is a free and open source…
43 min
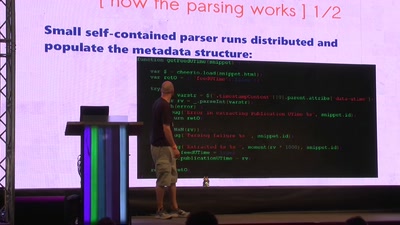
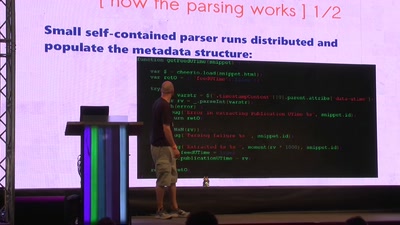
facebook.tracking.exposed

39 min
How the Internet is impacting organizing and dissent in…
48 min
Retro-gaming on open hardware

41 min
How to make use of democratic elections for your own purpose
44 min
Cracking DES nearly 20 years after the EFF DES Cracker
46 min
THE ALGORITHMIC PUBLIC SPHERE AND YOU

38 min
How to build alternative controllers
25 min
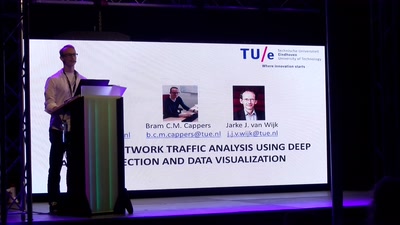
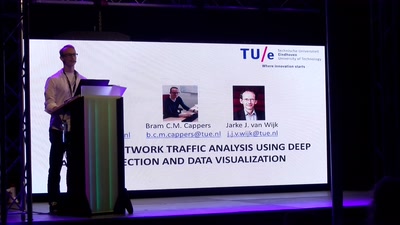
Eventpad: the Sublime editor for network traffic
18 min
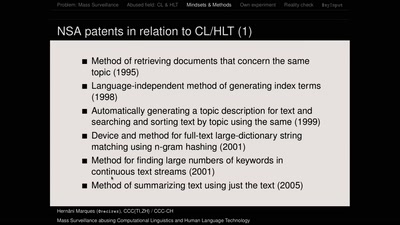
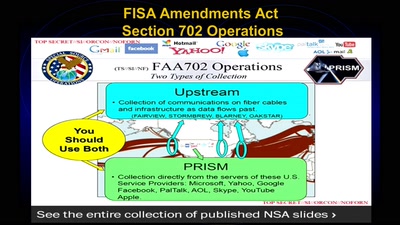
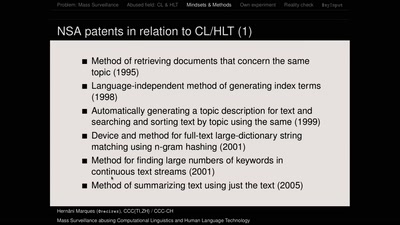
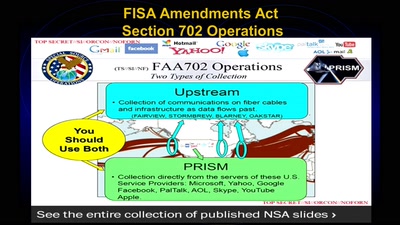
How Universities in the US collaborate with the United…
61 min
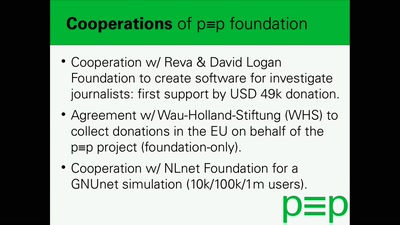
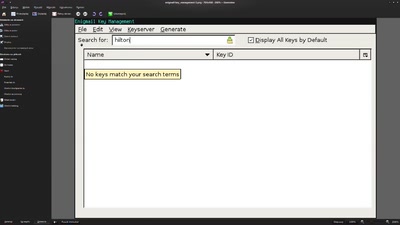
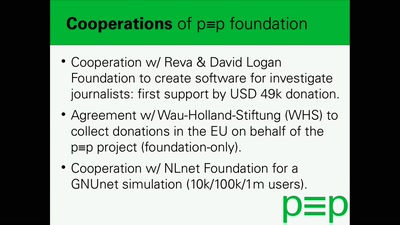
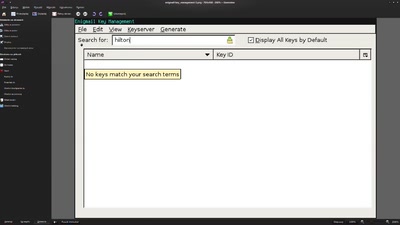
Easy to use automatic encryption for the masses
51 min
An authentication protocol that offers security, privacy…
29 min
are you not curious now? ;)
34 min
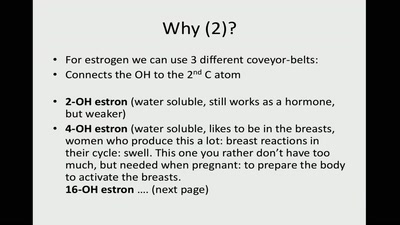
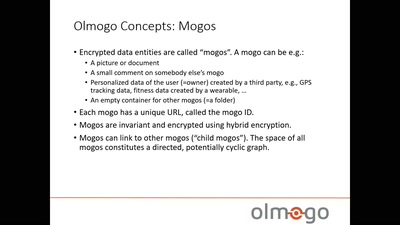
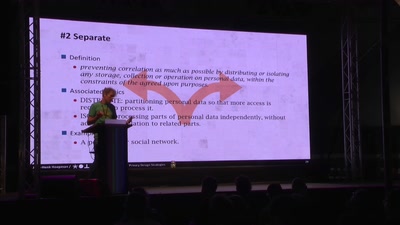
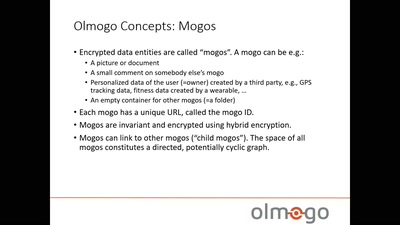
New paradigm in handling personal (health) data
57 min
What it means to profit from privacy-friendly, open-source…

59 min
The government is here to help
53 min
ensuring civil rights in the digital era
39 min
Keeping Secrets On Remote Machines
61 min
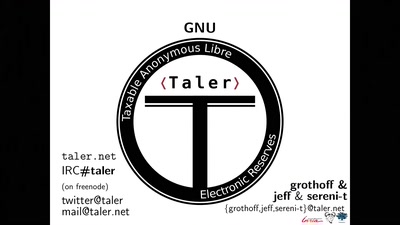
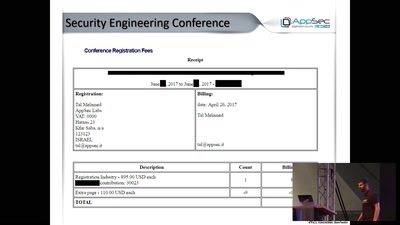
Independent One-Click Payments!

32 min
empower kids and provide tools for them to be more secure…
45 min
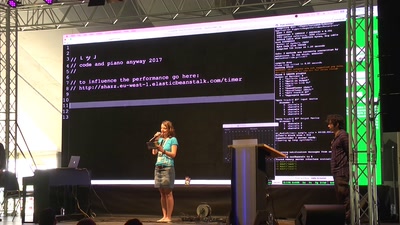
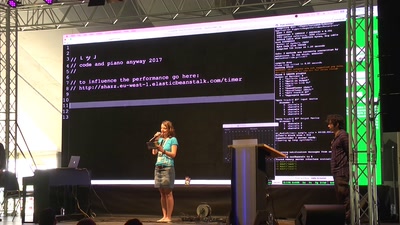
“Code Our Glance” and beta “CodeKlavier”
48 min
FLOSS, NGOs, Activists, Journalists, and the Pareto…

55 min
Implementation, hazards and updates on use of RNGs in…
48 min
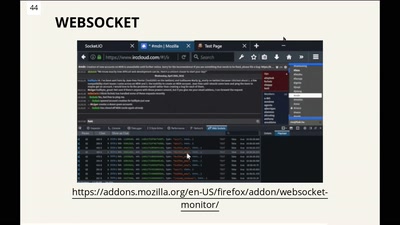
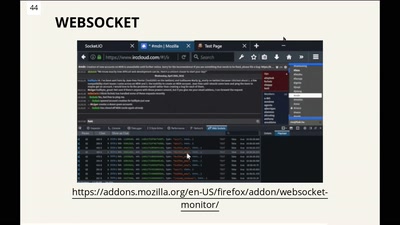
Do you know what you can do with Firefox for frontend…
60 min
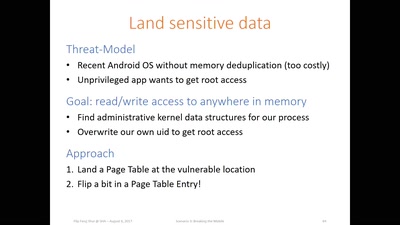
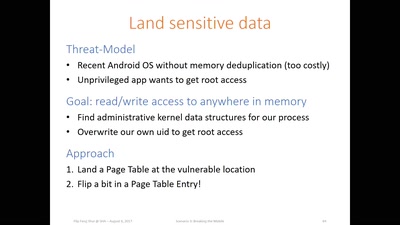
Advanced Rowhammer exploitation on cloud, desktop, and…
50 min
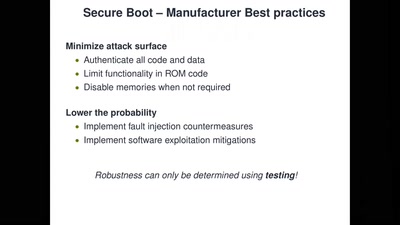
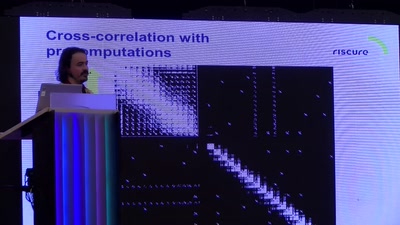
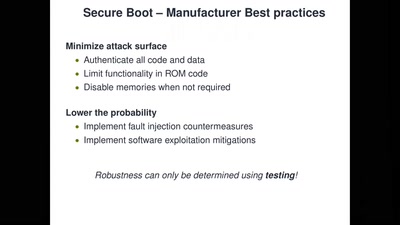
Bypassing Secure Boot using Fault Injection
47 min
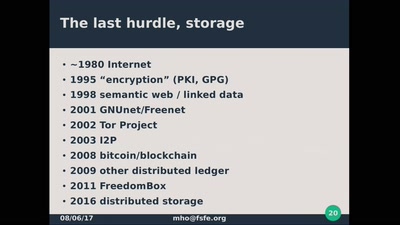
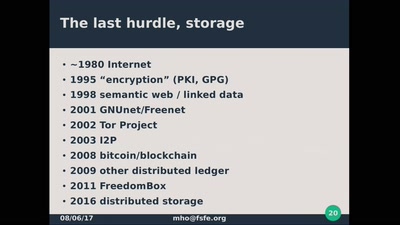
act up on decentralization
64 min
experimental, educational and commercial fermentation…

27 min
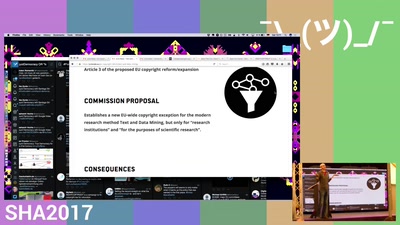
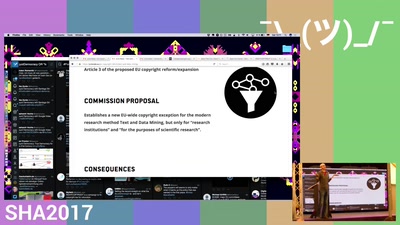
In what ways can laws influence the security of society.
61 min
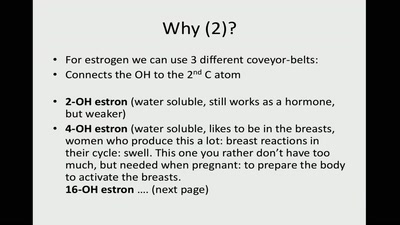
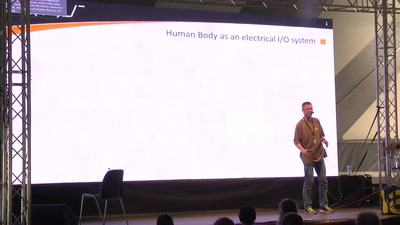
Hacking your brain, and other body parts. Debunking myths…

28 min
Modern Day American Hobo-ism
63 min
how your digital doppelganger has been exploiting you all…
40 min
How to re-enact a 1982 network art performance
47 min
A cryptographically secure social network platform

37 min
Why MissingMaps saves lives, and how to help
52 min
It's all fun and games until reality starts kicking you in…
74 min
If you like untaxed links and unsurveilled uploads, you…
141 min
TEETH, Hippis from Hell, Them F*cking Robots
33 min
How the reputation economy is turning us into conformists
30 min
When reality beats science fiction

50 min
Not only hackers do Security, Privacy and Hacking. Want to…
156 min
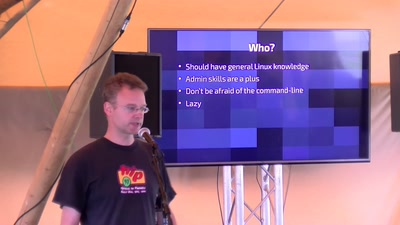
The legendary workshop that teaches you how network really…

50 min
towards edible network infrastructures
52 min
Doing well is good enough
59 min
Mind-sets, state-of-the-art methods and practices according…
36 min
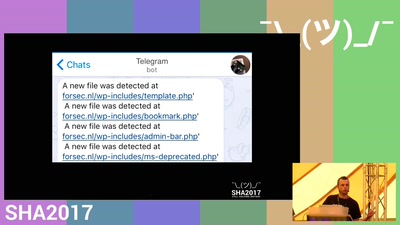
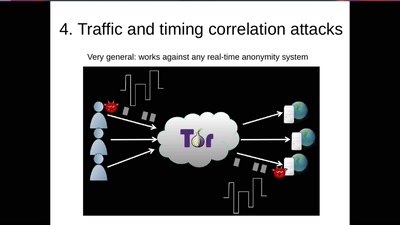
Using TOR for securing Smart Homes from prying eyes

64 min
Current case studies of whistleblowing in Europe, and how…
61 min
How people have lost their anonymity? Let's study…
53 min
Checkpoint on the road towards inevitable
61 min
Surprise: it is fully digital!
58 min
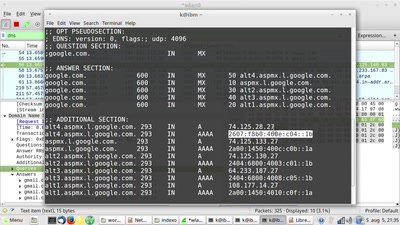
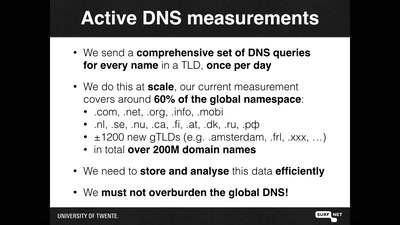
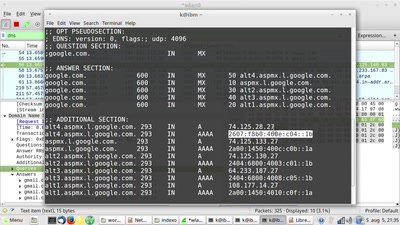
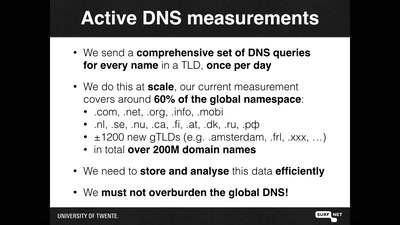
I measured 60% of the DNS, and I found this
40 min
Free and open source software has far too many security…
38 min
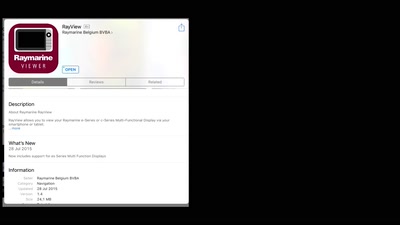
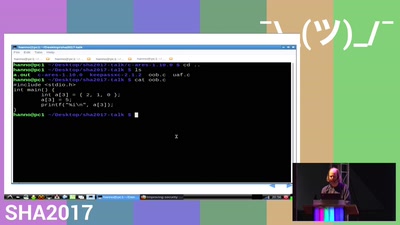
Fun with onboard maritime systems
57 min
It's not only Hollywood who is out of ideas
41 min
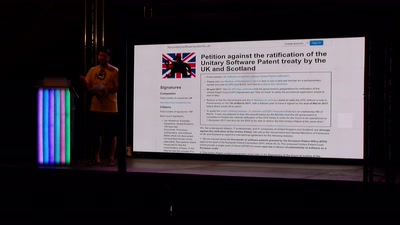
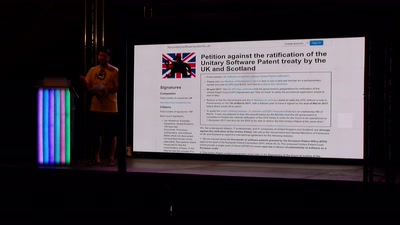
Have we silently lost the battle against software patents…
23 min
Heaven is imperfect by design
59 min
Perspective from the inside
62 min
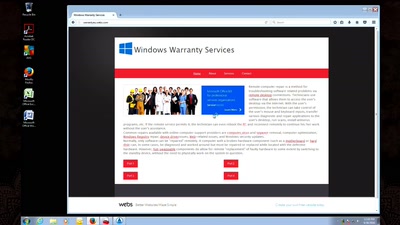
Hunting down a criminal call center
23 min
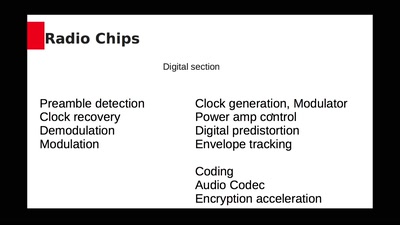
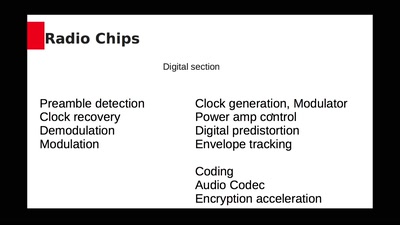
World radio spectrum domination through silicon control
53 min
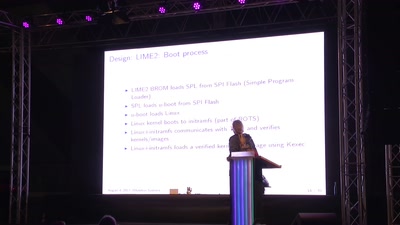
NLNet sponsored (open hardware) trusted boot module

33 min
How can we make sure that young people's voices are heard…
![NSFW: Di[CENSORED]s for privacy](https://static.media.ccc.de/media/events/SHA2017/49-hd.jpg)