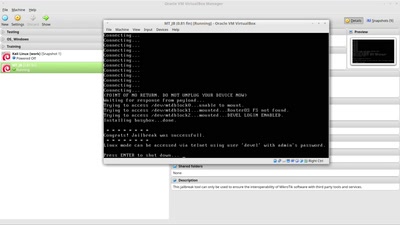
More and more (secure) embedded systems implement a feature to assure the integrity and confidentiality of all software executed after power-on reset, commonly referred to as secure boot. When not logically flawed, other attack techniques must be used to bypass the provided security. Such an attack technique is fault injection.
#DeviceSecurity