Search for "Jossi"
next

55 min
Artists (mis)using technology
44 min
Tech unexeptionalism and the monopolization of every…
29 min
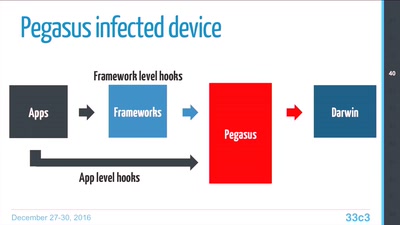
Technical Teardown of the Pegasus malware and Trident…

37 min
Don't ask what you can do for TPMs, Ask what TPMs can do…

32 min
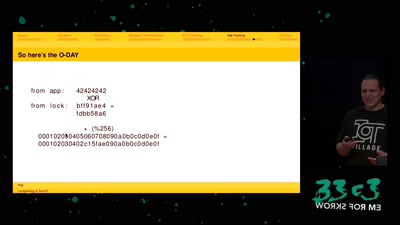
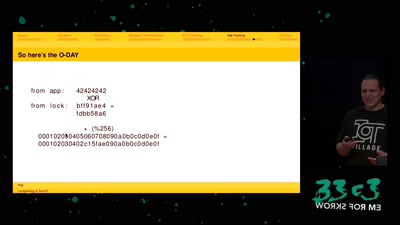
Automatic detection of key-reuse vulnerabilities

46 min
--Gaining code execution using a malicious SQLite database
60 min
...or why adding BTLE to a device sometimes isn't smart at…
58 min
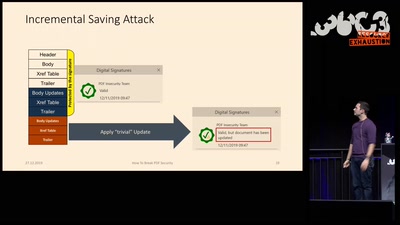
Breaking PDF Encryption and PDF Signatures
60 min
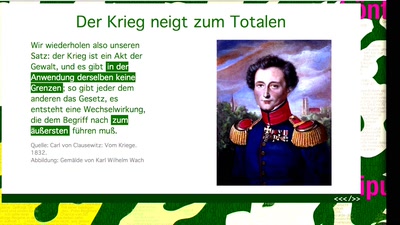
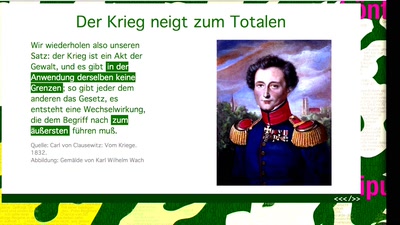
Operative Kommunikation im digitalen Informationskrieg
next