Search for person "Werner Van Belle" returned 150 results
87 min
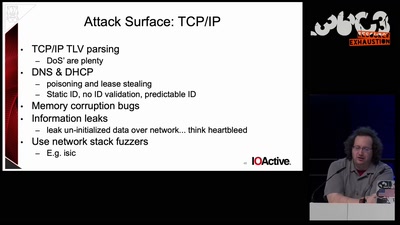
DNS privacy and security
Chaos Colloquium #1

63 min
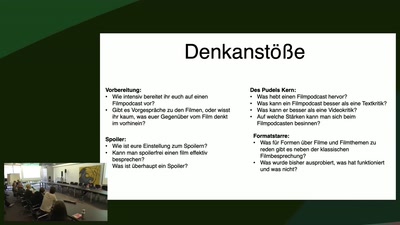
LightKultur in Deutschland
Clubkultur oder wie modern ist unser Kulturbegriff?
46 min
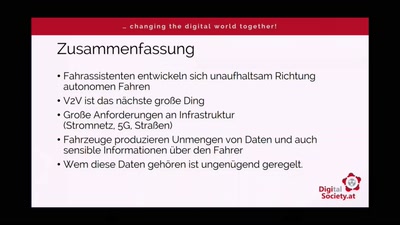
Datenschutz und Mobilität
Reisefreiheit im digitalen Zeitalter

25 min
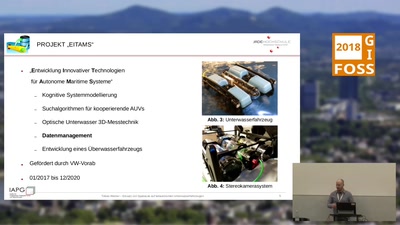
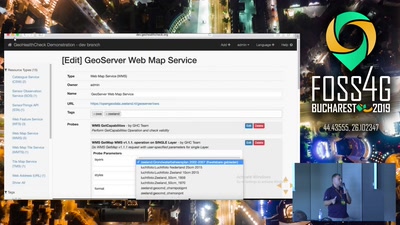
GeoHealthCheck
Uptime and QoS monitor for geospatial web-services
58 min