16 min
Bypassing Enterprise Policy in Firefox

20 min
Unleashing Reinforcement Learning in Penetration Testing…
21 min
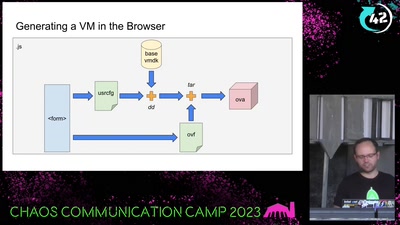
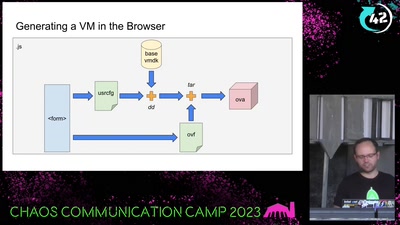
Building disposable Windows VMs
29 min
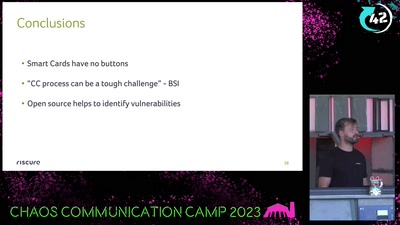
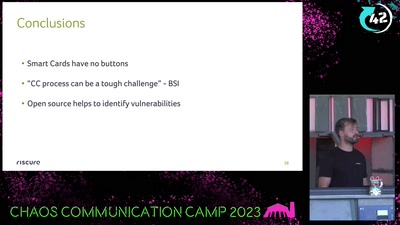
Attacking an opensource U2F device in 30 minutes or less

39 min
Insights into the hardware and software of sounding rockets
41 min
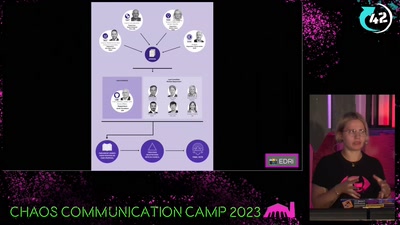
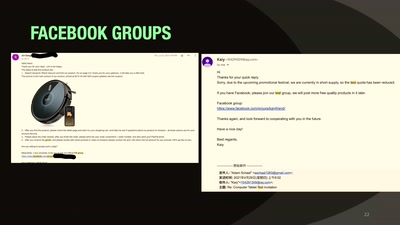
And the malware and backdoors that came with it.
43 min
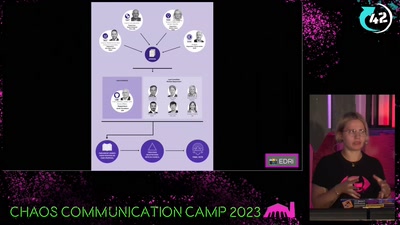
now is the time to take action!
43 min
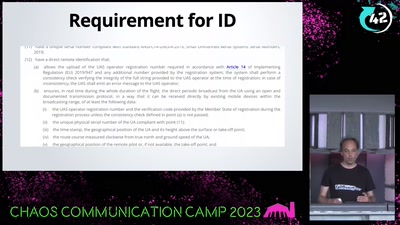
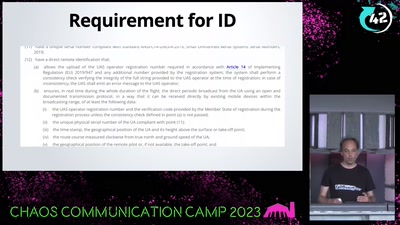
A hacker's view at commercial drone security
43 min
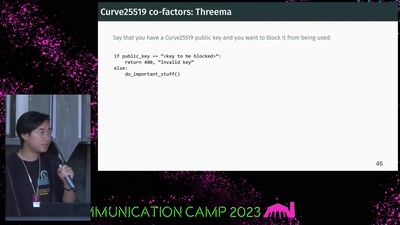
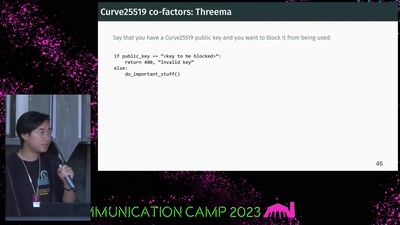
Building Modern Cryptography
47 min
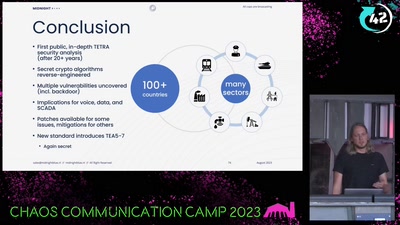
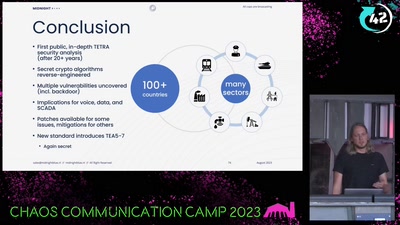
Obtaining the secret TETRA primitives after decades in the…

48 min
the superior Multi Factor Authentication Framework
61 min
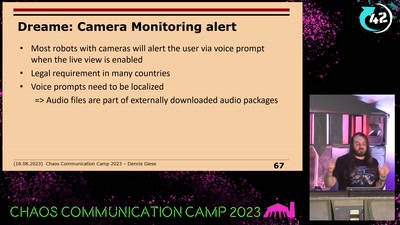
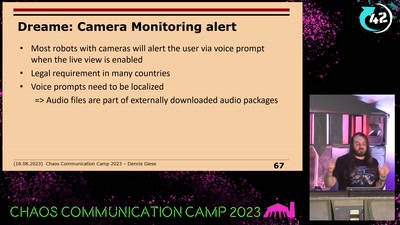
prevent your robot from sucking your data