30 min
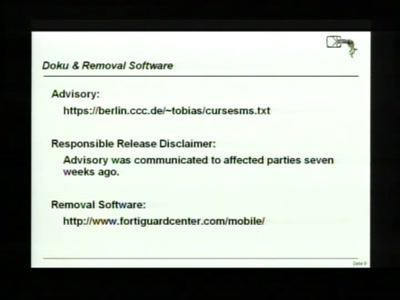
Accepting the Partial Disclosure Challenge
35 min
A clever or ingenious device or expedient; adroit…
38 min
How to get useable information out of your honeypot

44 min
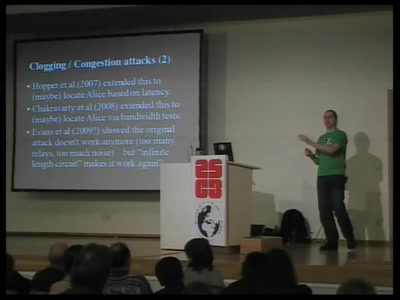
Building an anonymous Internet within the Internet
46 min
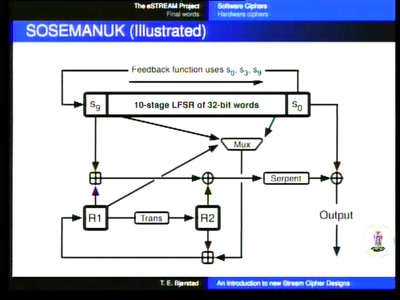
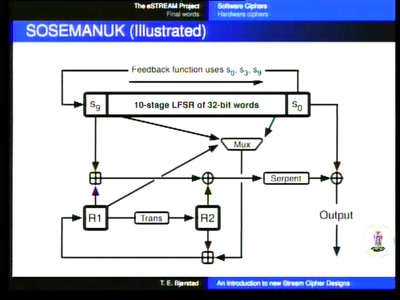
Turning data into line noise and back

48 min
Hide and Seek in A. Flash
48 min
Reverse Engineering von 3D-Dateiformaten
50 min
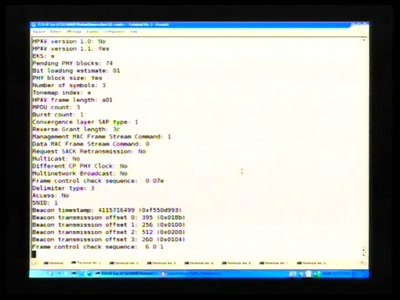
PowerLineCommunications has now their open source tool

50 min
Open source BIOS replacement with a radical approach to…

56 min
Is implementation the enemy of design?
56 min
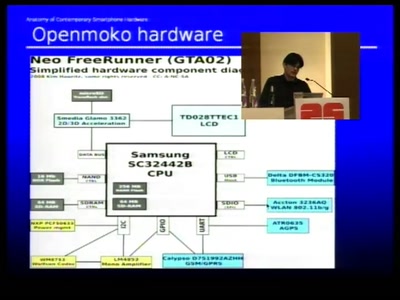
Dissecting contemporary cellphone hardware
58 min
Pwning Apple's Mobile Internet Device
58 min
Recovering keys and other secrets after power off

58 min
Tampering the Tamper-Proof
61 min
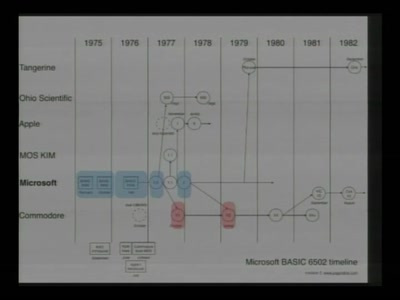
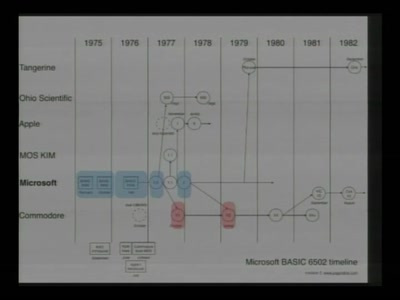
Everything about the C64 in 64 Minutes

61 min
Bestandsaufnahme und Auswirkungen

61 min
Essentielles Grundwissen für alle, die nichts zu verbergen…
61 min
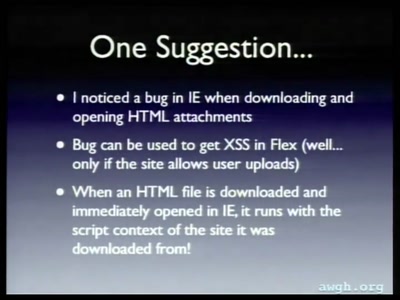
Not your mother's XSS bugs
61 min
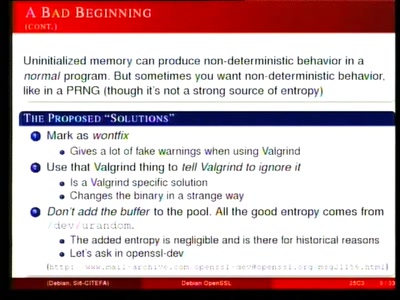
Creating a rogue CA Certificate
62 min
Past, present, and future
63 min
Symbian Exploit and Shellcode Development
63 min
Overview of Current Keylogger Threats

65 min
Behind the scenes of the new light installation
66 min
The Digital Enhanced Cordless Telecommunications standard

76 min
Breaking Remote Keyless Entry Systems with Power Analysis
82 min
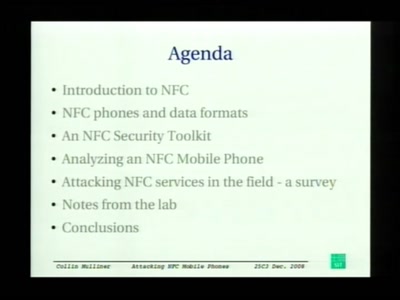
First look at the security of NFC mobile phones
92 min
Or: about what we will laugh next year
94 min
Oder: worüber wir nächstes Jahr lachen werden