Henryk Plötz and Milosch Meriac
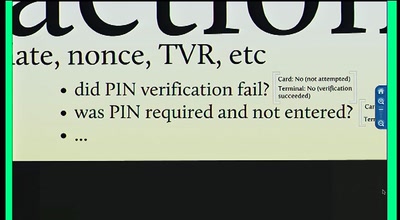
Popular contactless systems for physical access control still rely on obscurity. As we have shown, time and time again, proprietary encryption systems are weak and easy to break. In a follow-up to last year's presentation we will now demonstrate attacks on systems with 'proper' cryptographic algorithms.