Search for "seda"
prev

63 min
Artistic interventions in climate change
54 min
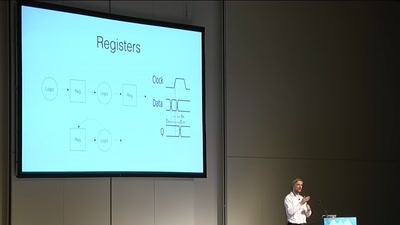
Making awesome stuff with FPGAs
62 min
Building a space for grassroots sustainable technology…
58 min
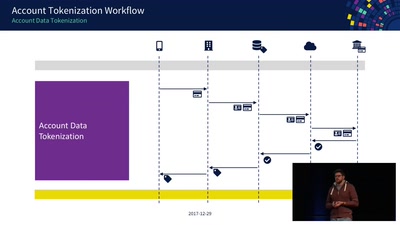
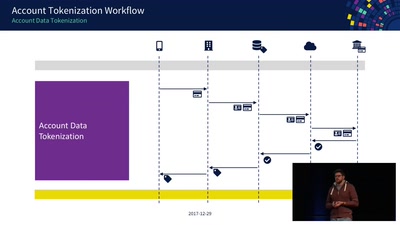
An Exploration of NFC Transactions and Explanation How…
60 min
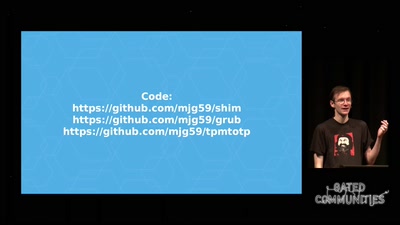
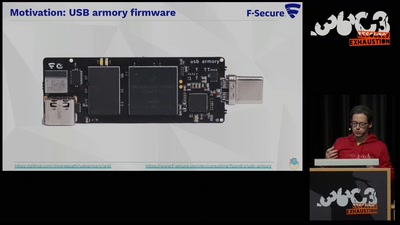
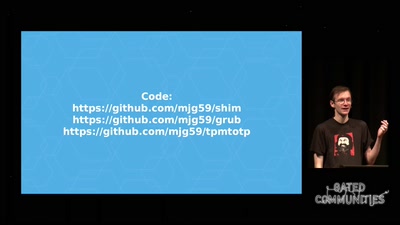
Making it easier to avoid low-level compromise, and why…
57 min
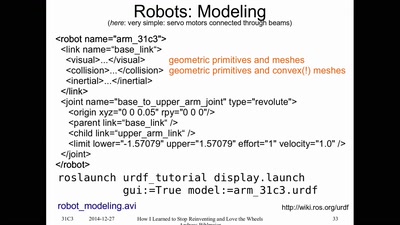
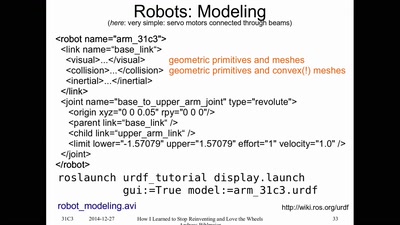
or having FUN with (home/hackerspace) robotics
59 min
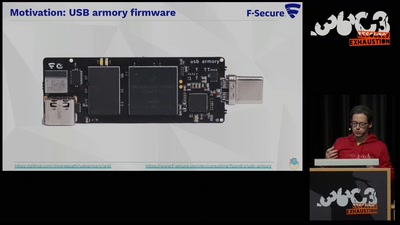
Reducing the attack surface with pure embedded Go.
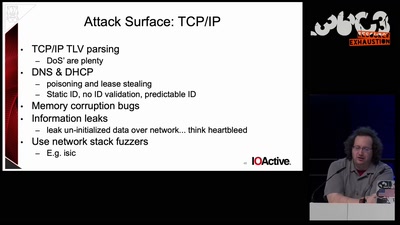
62 min
Auditing Boot Loaders by Example
55 min
The role of social-graphs for Drones in the War on Terror.
61 min
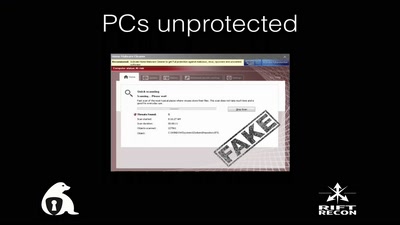
Exploitation in a new media
60 min
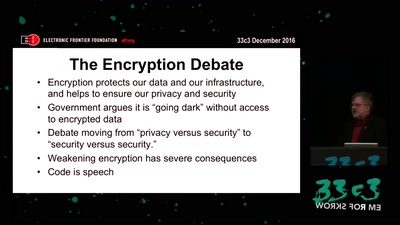
Crypto fight in the Wake of Apple v. FBI
61 min
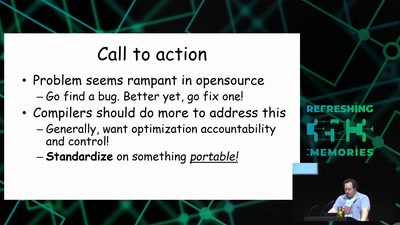
why clearing memory is hard.
60 min
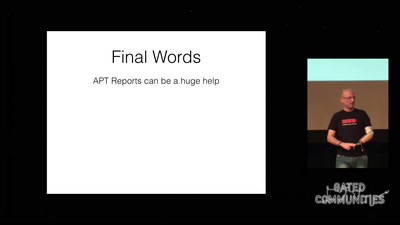
How advanced threat actors learn and change with innovation…

61 min
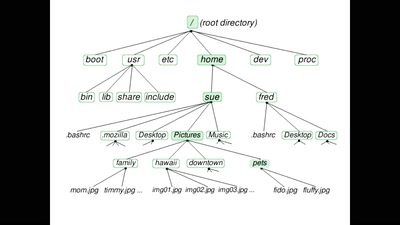
fun(ctional) operating system and security protocol…
58 min
Physically Unclonable Functions for Hardware Tamper…
prev