Search for person "Elke Steven" returned 22 results

39 min
Neuroexploitation by Design
Wie Algorithmen in Glücksspielprodukten sich Wirkweisen des…
60 min
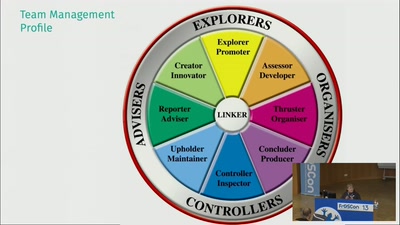
12 years as QA in Agile Teams - what has worked and what hasn't
Tales and experiences with people, ways of working, and…
41 min
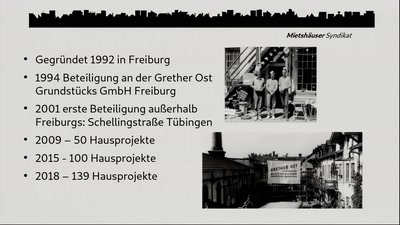
Die Häuser denen, die darin wohnen!
Langfristig bezahlbares, gemeinsames „Mieteigentum“…
57 min
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol

58 min
Security Failures in Smart Card Payment Systems
Tampering the Tamper-Proof
62 min
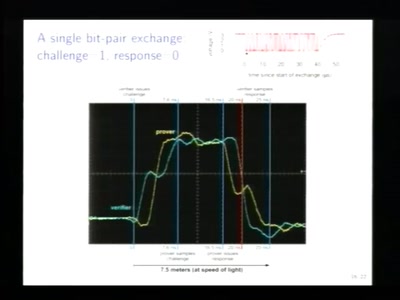
Relay attacks on card payment: vulnerabilities and defences
Keeping your enemies close

62 min
Detecting temperature through clock skew
Hot or Not: Defeating anonymity by monitoring clock skew to…
42 min
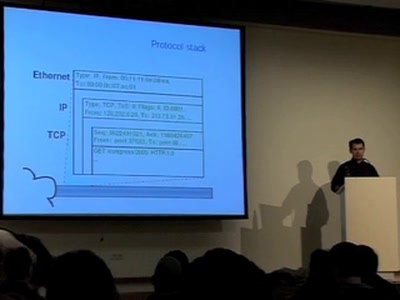
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
45 min