Search for person "Paul van Genuchten" returned 197 results

63 min
LightKultur in Deutschland
Clubkultur oder wie modern ist unser Kulturbegriff?

55 min
Netzphilosophische Matinée
Ein Hirnlüfter der Dresdner Technikphilosophie.…
61 min
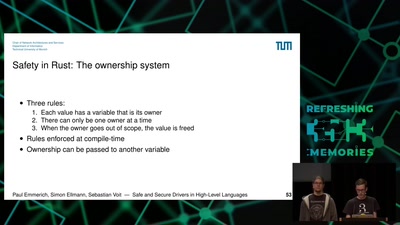
Safe and Secure Drivers in High-Level Languages
How to write PCIe drivers in Rust, go, C#, Swift, Haskell,…

25 min
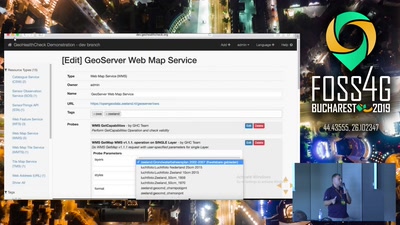
GeoHealthCheck
Uptime and QoS monitor for geospatial web-services
58 min
Are all BSDs created equally?
A survey of BSD kernel vulnerabilities.

44 min
Life Needs Internet
Documenting digital culture through handwritten letters
53 min
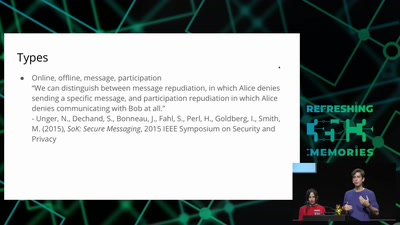
Smart, safe & happy
ensuring civil rights in the digital era
31 min