Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention technology
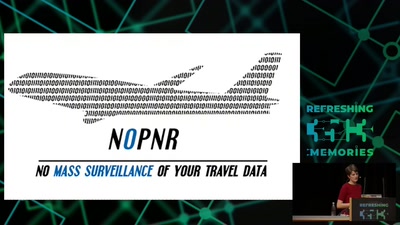
The deepening of global Internet infrastructure comes accompanied with an invigorated capacity and intent by adversaries to control the information that flows across it. Inextricably, political motivations and embedded power structures underlie the networks through which we interpret and understand our societies and our world - censorship threatens the integrity of the public sphere itself. The increasing technical sophistication of information controls deployed by censors in adversarial network environments around the world can be uniquely viewed and researched by circumvention tool providers, whose work continues to preserve access to the open Internet for all communities. Through this presentation, we endeavour to share insights gained from the front lines of this technical contest.
The deepening of global Internet infrastructure comes accompanied with an invigorated capacity and intent by adversaries to control the information that flows across it. Inextricably, political motivations and embedded power structures underlie the networks through which we interpret and understand our societies and our world - censorship threatens the integrity of the public sphere itself. The increasing technical sophistication of information controls deployed by censors in adversarial network environments around the world can be uniquely viewed and researched by circumvention tool providers, whose work continues to preserve access to the open Internet for all communities. Through this presentation, we endeavour to share insights gained from the front lines of this technical contest.
The following key questions will be answered in this session:
- What are circumvention tools conceptually and how do they work?
- How have the techniques of adversaries evolved?
- What are the latest innovations in circumvention technology?
- How have emerging economies been affected, where censorship and and surveillance hardware and software are built-in to newly established ICT infrastructure?
- How do circumvention trends follow censorship events and social/political movements?
- Where do we see these technical advances leading the next generation of censorship and circumvention technology?
This is a Foundations talk. No prior understanding of circumvention technology is required to enjoy this, but the presentation will hopefully be enjoyable to all experience levels.
https://papers.ssrn.com/sol3/papers.cfm?abstract_id=3244046
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.