Search for "M" returned 12027 results
59 min
Top X* usability obstacles
*(will be specified later based on usability test with…
62 min
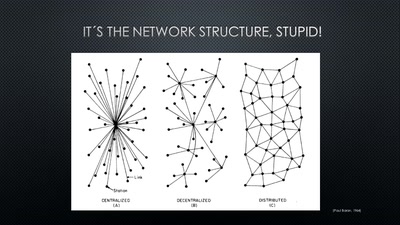
A New Kid on the Block
Conditions for a Successful Market Entry of Decentralized…
60 min
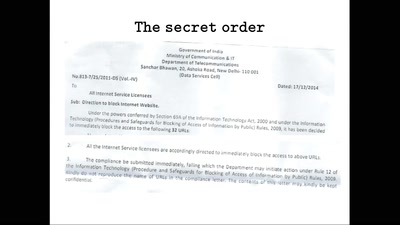
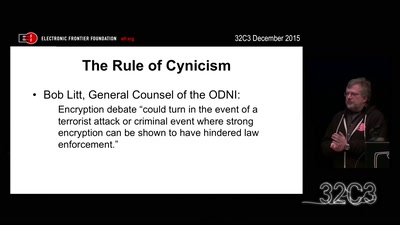
Crypto Wars Part II
The Empires Strike Back

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
57 min
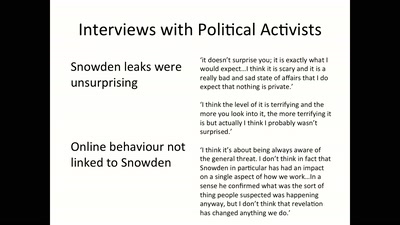
“I feel like a criminal and I have to be god at the same time”
Perceptions of hackers and hacktivists on their…
44 min
Replication Prohibited
3D printed key attacks
95 min
Hacker Jeopardy
Zahlenraten für Geeks
32 min
Technology and Mass Atrocity Prevention
Overview on Current Efforts - We Need Moar H4x0rs?!
27 min
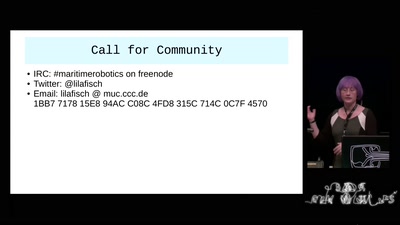
Maritime Robotics
Hackers, I call thee to our Oceans!
30 min
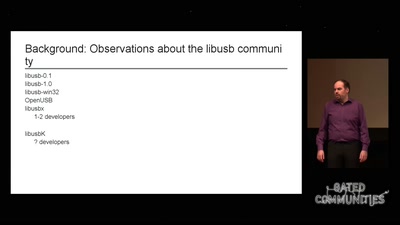
libusb: Maintainer fail
How I failed to run an open source project
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science

60 min
Österreich: Der Kampf gegen unkontrollierte Massenüberwachung
Geheimdienste kontrolliert man am besten, indem man ihre…
29 min
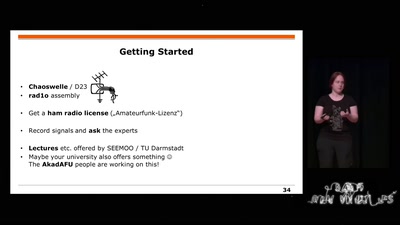
Building and Breaking Wireless Security
Wireless Physical Layer Security & More...

60 min
Stromtankstellen – eine neue öffentliche Infrastruktur
Was kann das? Wie kann ich das nutzen? Wo besteht…

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research

60 min
the possibility of an army
phone verified accounts bringing the Hessian army back to…
60 min
Internet Cube
Let's Build together a Free, Neutral and Decentralized…

22 min
Trust us and our business will expand!
Net-activism strategies against fake web companies

60 min
Free Software and Hardware bring National Sovereignty
Gaza as a case study
60 min
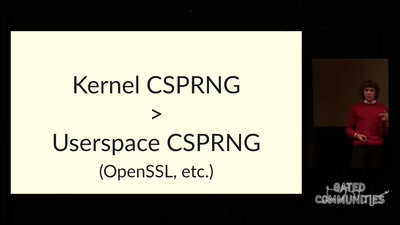
The plain simple reality of entropy
Or how I learned to stop worrying and love urandom
60 min