Search for "Thore"
prev
next
30 min
How to educate society through the language of art
58 min
A survey of BSD kernel vulnerabilities.

36 min
Hardware implants in the supply-chain
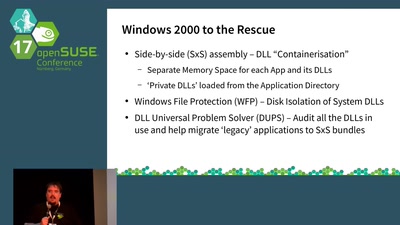
38 min
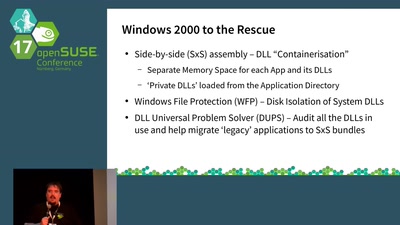
What should we do about Containerised Applications?
35 min
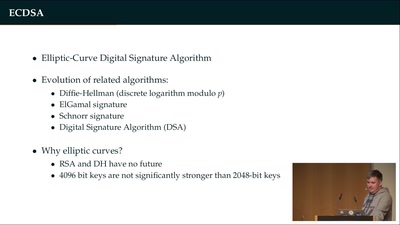
How (not) to protect private keys
54 min
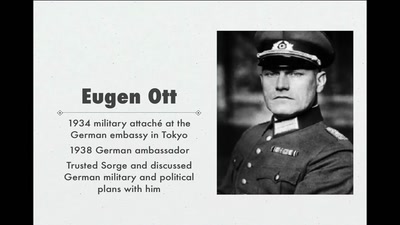
Stalin's best men, armed with paper and pen
49 min
How the Btx hack changed computer law-making in Germany
prev
next