Search for person "Roland van Rijswijk-Deij" returned 165 results
53 min
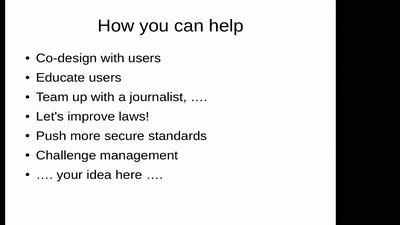
Smart, safe & happy
ensuring civil rights in the digital era
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
42 min
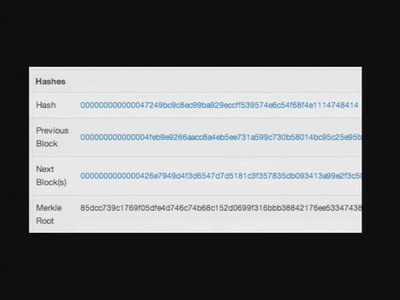
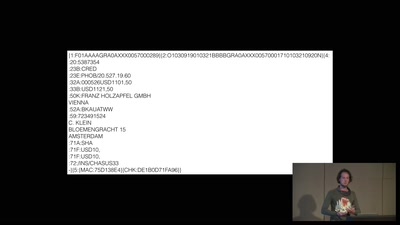
A world without blockchain
How (inter)national money transfers works
27 min
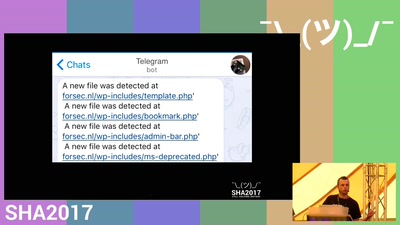
Detecting a breach from an attackers perspective.
We're gonna regret this
23 min
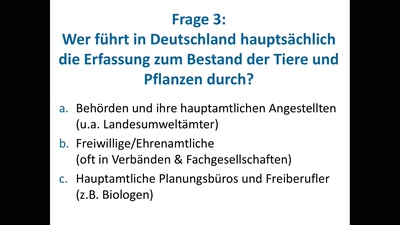
OpenSource, OpenData und Citizen Science in der Biodiversitätsforschung
Wie Wissenschaft und Verwaltung von freiem Zugang und…
60 min
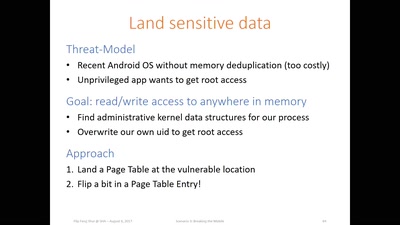
Flip Feng Shui
Advanced Rowhammer exploitation on cloud, desktop, and…
63 min
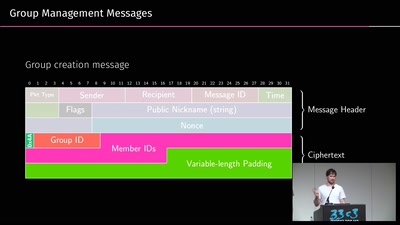
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
53 min
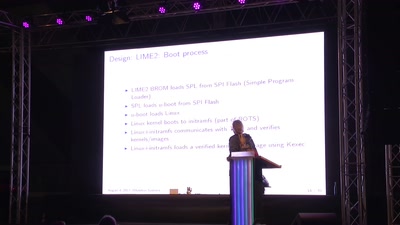
TBM: Trusted boot module
NLNet sponsored (open hardware) trusted boot module
60 min
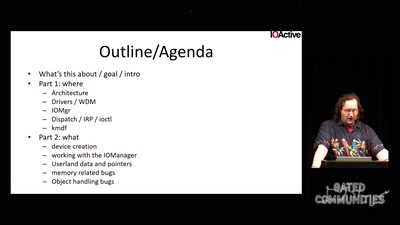
Windows drivers attack surface
some 'new' insights

61 min
Avoiding kernel panic: Europe’s biggest fails in digital policy-making
How the institutions fuck up, and how we fuck it up as well
45 min
Time affects
Human-computer-synchronizations

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
28 min
Long war tactics
or how we learned to stop worrying and love the NSA
29 min
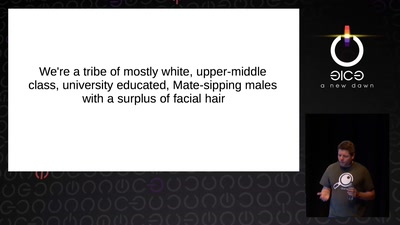
Infocalypse now: P0wning stuff is not enough
Several failure modes of the hacker scene
61 min
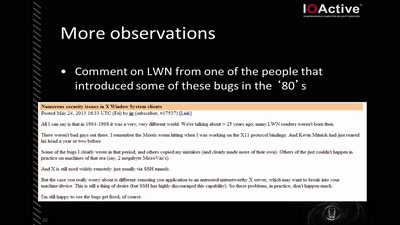
X Security
It's worse than it looks
61 min
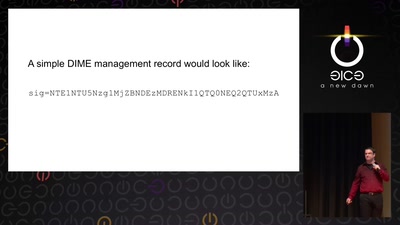
Now I sprinkle thee with crypto dust
Internet reengineering session
58 min