44 min
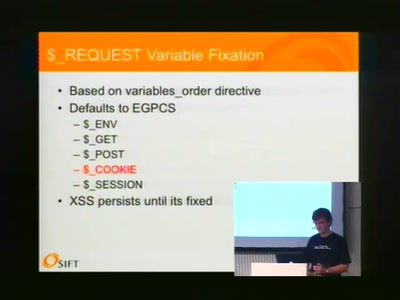
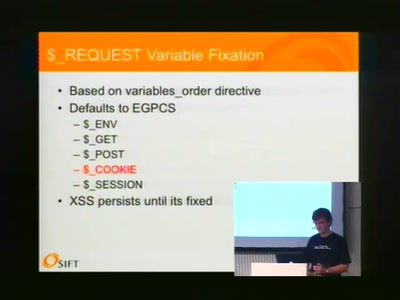
A Web Hacker's Bag O' Tricks
46 min
Look what I found under the carpet
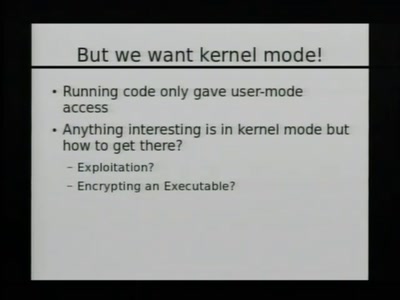
48 min
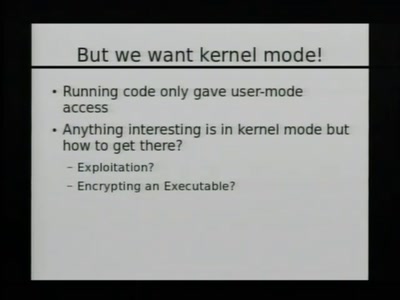
Post-Exploitation Fun in Windows Environments
90 min
Oder: worüber wir nächstes Jahr lachen werden
34 min
How In The End We Got It All!
52 min
A swiss army knife for automatic social investigation
62 min
Keeping your enemies close

42 min
A couple of stories about kernel exploiting
59 min
Typische Sicherheitslücken
50 min
An introduction into anonymous communication with I2P

44 min
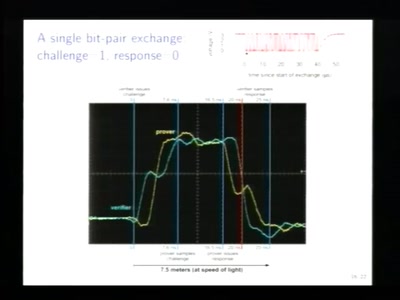
New ideas for old practices

57 min
Revisiting the legendary computer in a joystick
57 min
how to own critical infrastructures
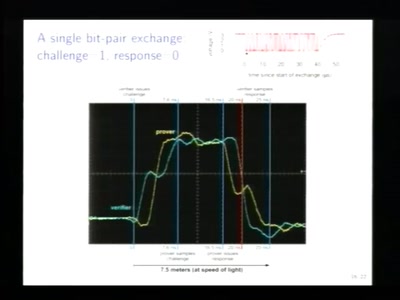
59 min
Little Security, Despite Obscurity

63 min
or how B.A.T.M.A.N. learned to fly

42 min
Practical VM exploiting based on CACAO

59 min
How to find that special one out of millions
53 min
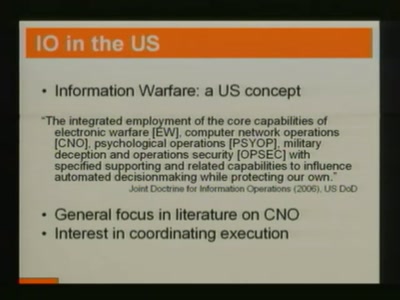
An analysis of targeted attacks from 2005 to 2007

75 min
We Track Harder - We Track More! Take the pain out of…

56 min
How to Hack the Pfandsystem