Understanding buffer overflow exploitation
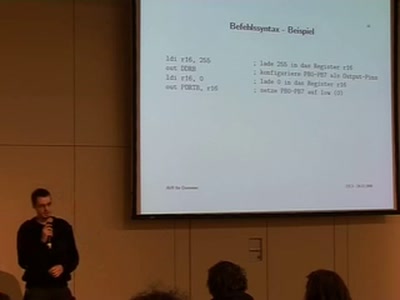
The fascinating interplay of CPU, stack, C-compiler and shellcode in a nutshell
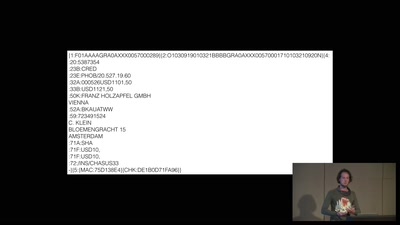
Everything started with Aleph One's paper "Smashing the Stack for Fun and Profit". These techniques are still the basis for modern exploitation of buffer, heap and format string vulnerabilities. We will give a swift overview about C functions, stack usage, assembler, gcc, gdb and how these few tools can be used to understand and write shell-code to turn simple buffer overflows into backdoors that open whole systems to potential attackers. Sure you want to know how to defend against that. We also will tell you about that!