Search for "Harm Delva"
next
19 min
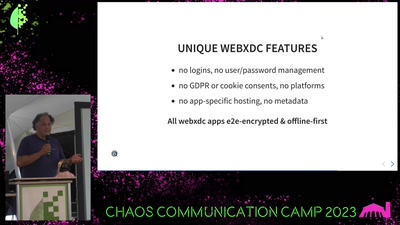
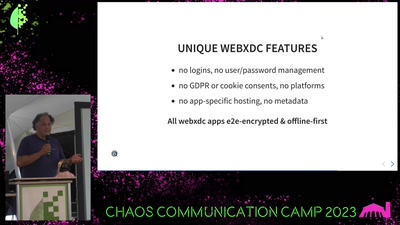
unlocking the potential of e-mail and the web
65 min
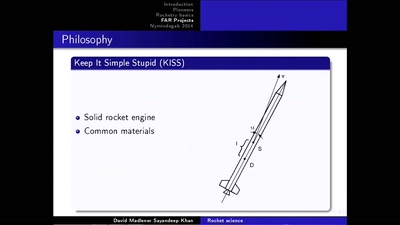
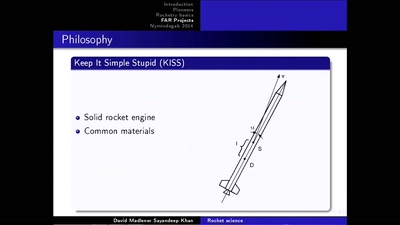
First steps into space with sounding rockets
59 min
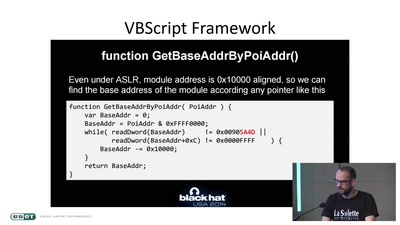
A Journey in the Land of (Cyber-)Espionage
35 min
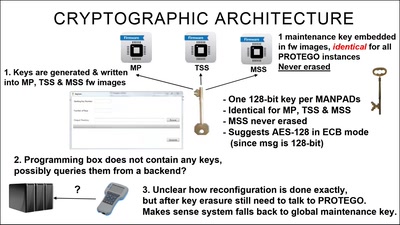
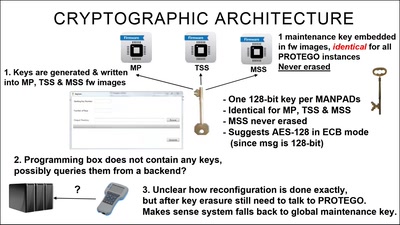
Taking a look at a covert CIA virtual fencing solution
46 min
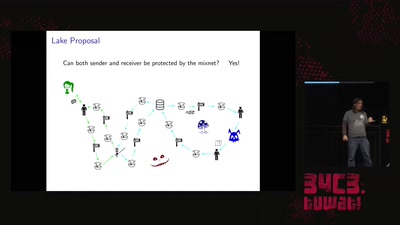
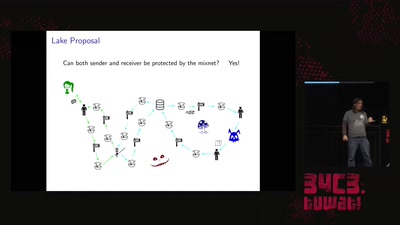
Strong metadata protection for asynchronous messaging
46 min
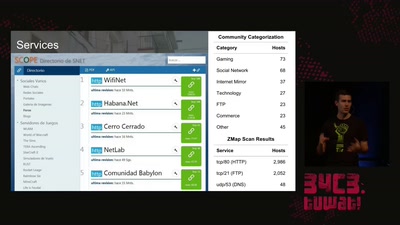
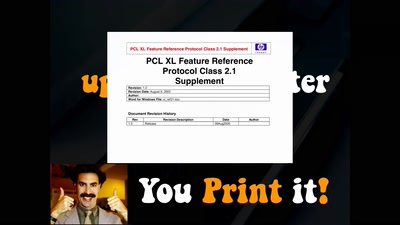
Hacking your network likes it's 1980 again
58 min
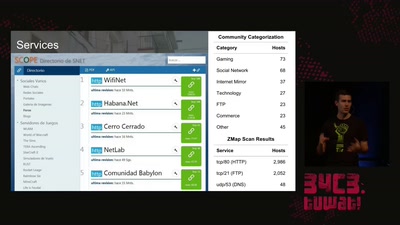
Get a unique tour of some of the world’s most unusual…

38 min
Estimating the costs of algorithms for attacks and defense…

63 min
Developing open, FPGA-based capture hardware for conference…
next