Search for "Ezi"
next

51 min
Abusing your Firmware to backdoor the kernel
27 min
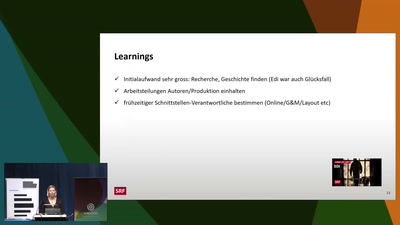
Eine wahre Geschichte neu erzählt
29 min
Hackers' knowledge studied by sociologist of science

41 min
Electrifying the Thread out of Clothing

50 min
Open source BIOS replacement with a radical approach to…
58 min
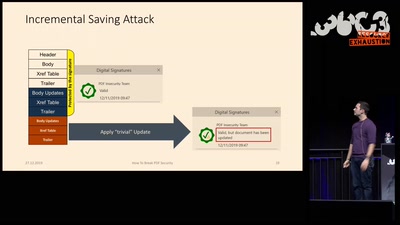
Breaking PDF Encryption and PDF Signatures
56 min
Reverse Engineering the Motorola EZX (A768,A780,E680)…
60 min
...or why adding BTLE to a device sometimes isn't smart at…

32 min
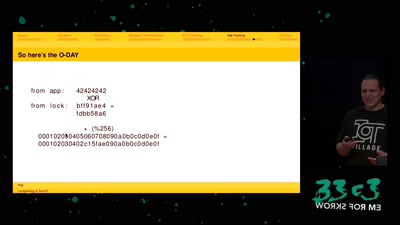
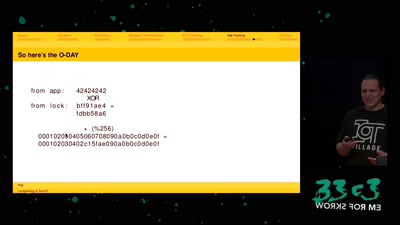
Automatic detection of key-reuse vulnerabilities
next